The Self-Encrypting Drives (SED) encrypt the data stored on them using internal key called Data Encryption Key (DEK). The data is encrypted while writing data to them and decrypted while reading data from them. They get locked on power cycle to provide data protection at rest. These drives need to be unlocked by providing an authentication key(AK) to read or write data to them. While disposing the drives, the data on them can be securely erased by changing the DEK. In some cases, organizations are compelled to use SED drives to meet some government policies like data protection at rest and secure erasing the drives before disposing them.
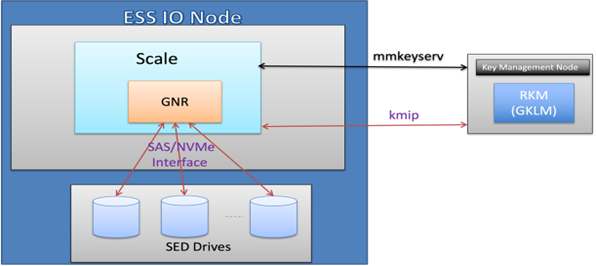
In ESS 6.1.5.0 the SED support is enabled as shown in the diagram below using a key, managed by external key manager like GKLM, as authentication key (AK) also known as Master Encryption Key(MEK) which adheres to FIPS 140-2 standards. The HDD and NVMe drives of ESS 3500 are enabled for SED support following TCG Enterprise Storage Subsystem Class and OPAL 2 Storage Subsystem Class specifications respectively. The IBM’s Spectrum Scale’s user friendly mmkeyserv command can be used to configure and setup the MEK. Once MEK is configured the SED support can be enabled on ESS 3500 system using mmvdisk sed enroll command. The MEK can be changed using mmvdisk sed rekey command, in case the MEK is compromised or need to change the key due to some key rotation policies. When SED is enabled the drives are crypto erased inherently as part of deleting the Recovery Group of the ESS system.
The details of mmkeyserv command to configure the MEK on remote key servers can be found at
https://www.ibm.com/docs/en/spectrum-scale/5.1.5?topic=reference-mmkeyserv-command
The details of mmvdisk sed command to enable SED support on ESS 3500 system can be found at
https://www.ibm.com/docs/en/ess-p8/6.1.5?topic=command-mmvdisk-sed
#Highlights-home#Highlights