In today's digital world, data is a critical aspect for any organization. Protecting and recovering data quickly from cyber threats has become key to drive businesses without interruption. Connecting systems online is inevitable to reach the end user directly. Cyber threats continue to increase as businesses opt for both digitalization and internet connectivity. These cyber threats can cause data theft or the loss of data for organizations and their clients, which can cause financial or reputational loss or more. Therefore, detecting threats in time as well as protecting and recovering data is crucial.
Data protection is an ever-evolving process because cybercriminals continuously invent new attack strategies. Consequently, defense mechanisms need to anticipate these next steps in order to remain secure. An effective protection plan requires two-part approach:
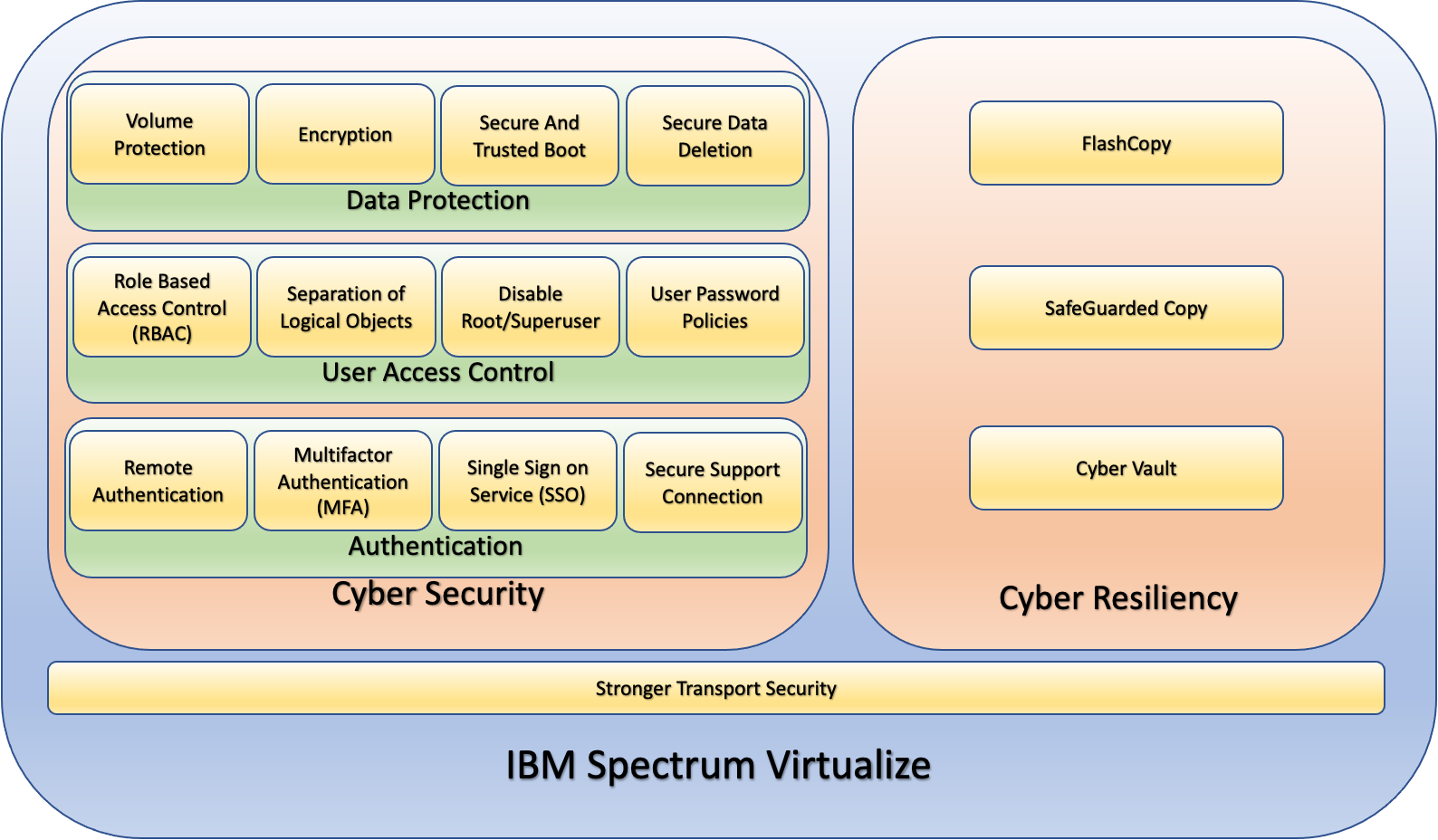
- Cyber Security. Cyber security is proactive approach to secure business data. It helps prevent attackers from obtaining access to the system in order to corrupt or steal data.
- Cyber Resiliency. Cyber resiliency is the mitigation mechanism to recover from cyber attacks when the cyber security mechanisms fail. It helps the organization recover data that has been encrypted, corrupted or deleted by an attacker. The processes and procedures of cyber resiliency are: to safeguard critical data; and use the safeguarded data to bring an organization back on track as soon as possible.
IBM Spectrum Virtualize is a software-defined storage ecosystem consisting of a highly flexible enterprise-class block storage solution. It can be deployed as a software on a client’s own infrastructure or can be purchased as a modular application. The software-based offering can be deployed on many cloud environments. IBM Spectrum Virtualize provides many enterprise-class features such as: compression; de-duplication; transparent cloud tiering; encryption; business continuity and data resiliency solutions; volume mirroring; storage virtualization and consolidation, et. al. IBM FlashSystem, IBM SAN Volume Controller and IBM Spectrum Virtualize for Public Cloud are all part of the IBM Spectrum Virtualize family of products.
IBM Spectrum Virtualize storage offers various features to configure Cyber security and Cyber resiliency at the storage level. These security features provides security at different levels as indicated in the following diagram.
Role-Based Access Control (RBAC)
IBM Spectrum Virtualize supports Role Based Access Control (RBAC). Users can create multiple user groups in IBM Spectrum Virtualize based upon their roles and tasks that they need to perform. Read-only access can be granted for monitoring and reporting staff. Copy services access can be given to application users to manage storage replication without making changes to system configurations. Administrator accounts can have full access to the logical configuration of the system. This granularity provides needs-based access to users.
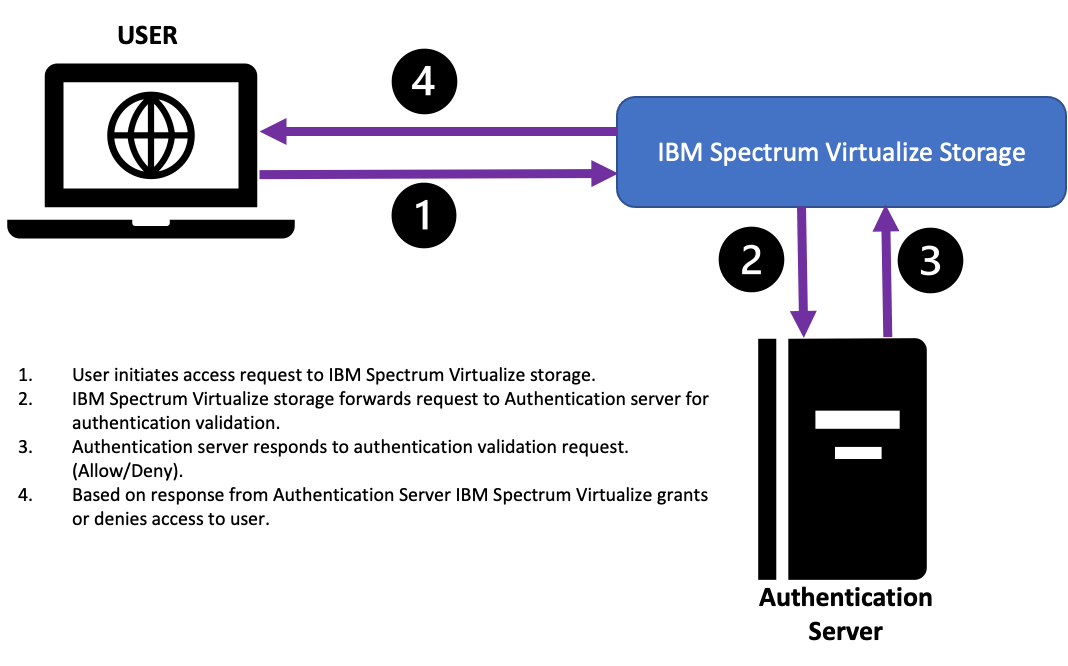
Remote Authentication
IBM Spectrum Virtualize storage can be integrated with an organization’s Lightweight Directory Access Protocol/Active Directory (LDAP/AD) for authentication. This allows central authentication and also enables efficient access history logging. Remote authentication supports the RBAC seamlessly. Local roles can be mapped to groups defined in the remote authentication server.
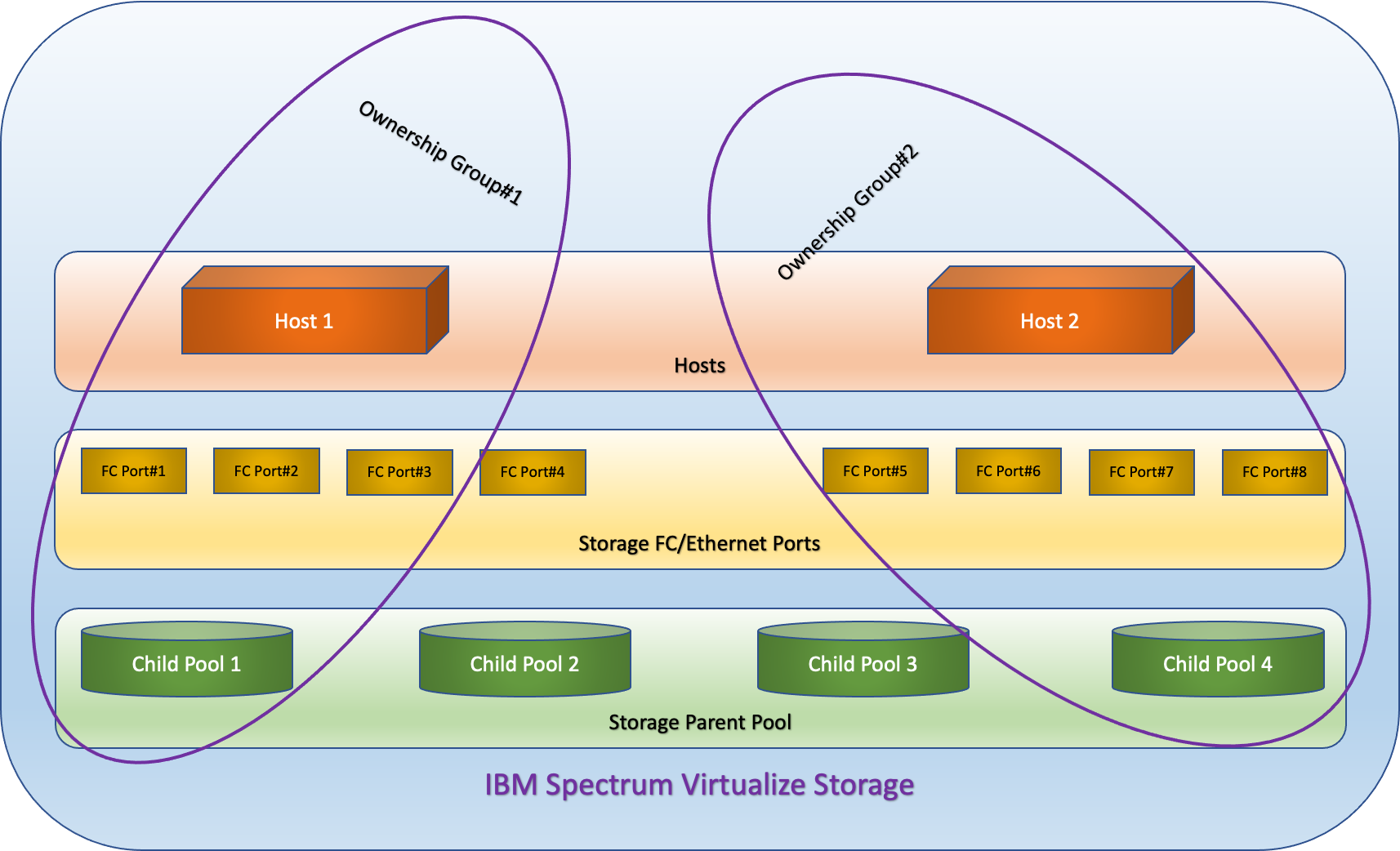
Separation of Logical Objects (Multi-Tenancy)
IBM Spectrum Virtualize offers an "Ownership Group" feature. By using this feature, a super user can create Ownership groups of logical objects within the storage. Every group can be assigned an independent administrator. An administrator of a group cannot manage or modify resources from a different group. This multi-tenancy feature provides additional layer of security between administrative users.
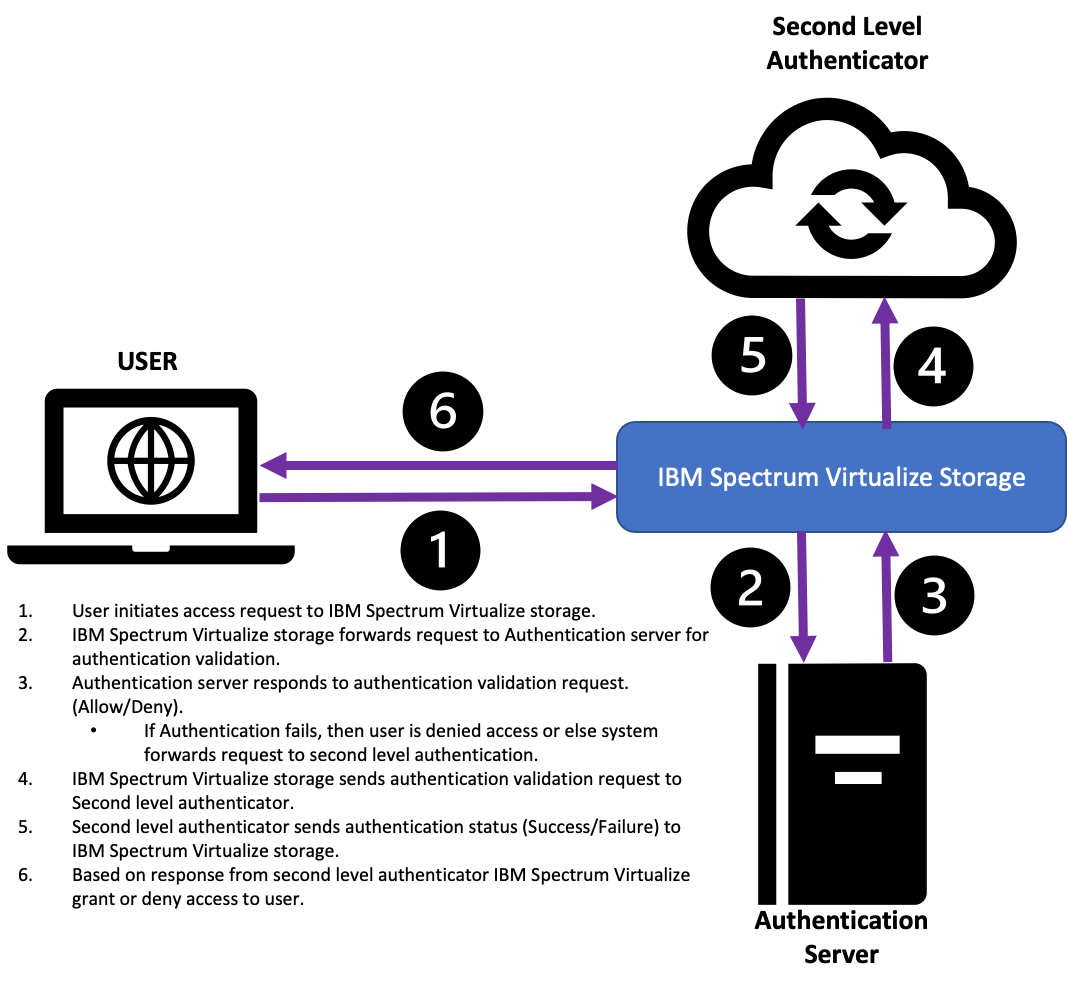
Multi-Factor Authentication
With the multi-factor authentication feature in IBM Spectrum Virtualize, a user can add an additional layer of security to avoid the breach of user credentials as the second-level authentication requires a user to enter either a one-time password or approve a push notification every time a user tries to authenticate their access.
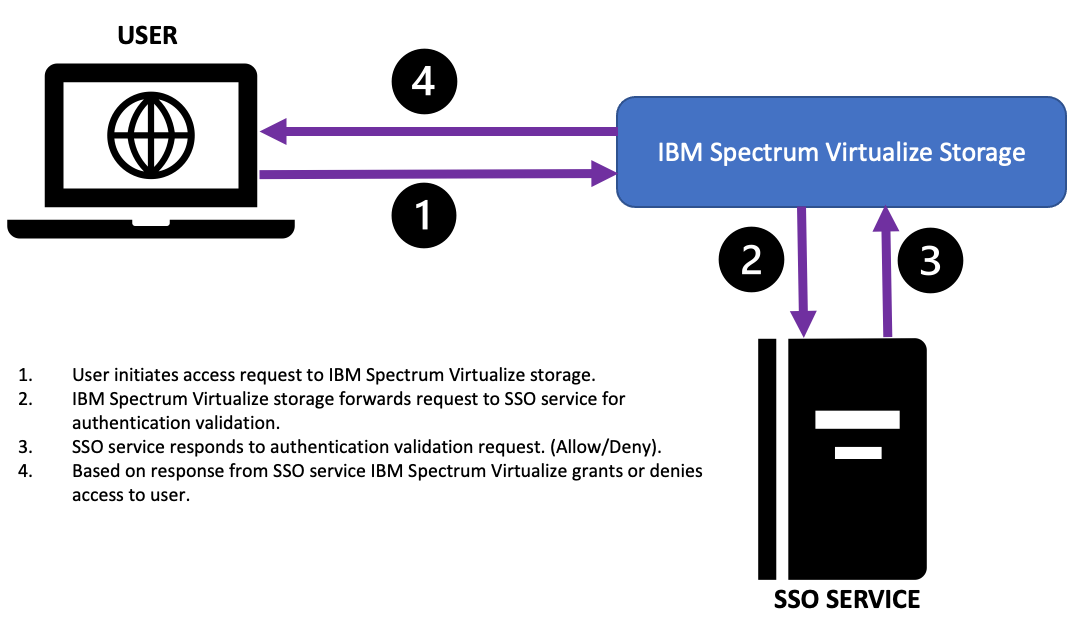
Single Sign-On Service (SSO)
The SSO feature in IBM Spectrum Virtualize directly integrates with the organization’s SSO service. This eliminates the need to create a user ID for every device.
Disable the Superuser/Root user
Disabling the superuser/root user helps prevent enabling full control of the storage to any user. This can be enabled or disabled only by physically accessing the system, which an attacker cannot do remotely.
Volume Protection
Volume protection prevents any volume deletion or unmapping of the volumes with active Inputs/Outputs (I/O) on it. So if an attacker tries to delete or unmap these volumes, the storage system will not allow it. This provides a window of protection after an unauthorized or unintentional change to the system occurs. The duration or time span can also be customized by the user.
User Password Policies
User password policies can be enforced to use strong and secure passwords. Different aspects of passwords can be controlled, such as the password length, character combinations, password reuse, password expiration and user locking policies. User accounts can be locked after multiple failed login attempts.
Encryption
IBM Spectrum Virtualize offers "data at rest" encryption. Even with physical system access, attackers cannot recover data. Data is encrypted using a secured algorithm. These encryption keys are maintained in the memory while the system is running. The encryption key is needed when an encrypted system boots, and the key can be provided physically via USB keys or directly from supported external key managers. The system and drive will not power on without a valid key. Supported encryption algorithms include the Advanced Encryption Standard (AES) algorithm with 256 bit symmetric encryption key as defined in IEEE 1619-2007 and NIST 800-38E.
Secure and Trusted Boot
The secure boot process in IBM Spectrum Virtualize encrypts and protects file systems on boot drives. The boot file system is protected by checksum when authorized code upgrades are committed to the boot disks. The system refuses to boot if any unauthorized change is detected on the file system. This can be caused by malicious changes or hardware errors. The system continues normally when known good code is available during the boot process.
Secure Data Deletion
IBM Spectrum Virtualize can securely delete data on drives using cryptographic erasure methods, block erasure or data overwrites. This function is natively available in the IBM Spectrum Virtualize software without any additional license.
Secure erase uses certified erasure algorithms that are compliant with European Regulation EU2019/424. This erasure can be performed on data and boot drives. Erased drives can be safely returned or decommissioned.
Secure Support Connection
The IBM support center can remotely access the system for faster troubleshooting and problem resolution. This remote access to IBM Spectrum Virtualize can be integrated with an organization’s proxy server. This secures incoming connections for remote support access. Based on the settings, an incoming support request can be authorized by the customer via the management graphical user interface (GUI).
Stronger Transport Security
IBM Spectrum Virtualize supports TLS 1.0 and TLS 1.2 for the management GUI traffic between the user’s browser and storage system. TLS 1.2 provides significant security enhancements over previous algorithms and mitigates against most man-in-the-middle threats.
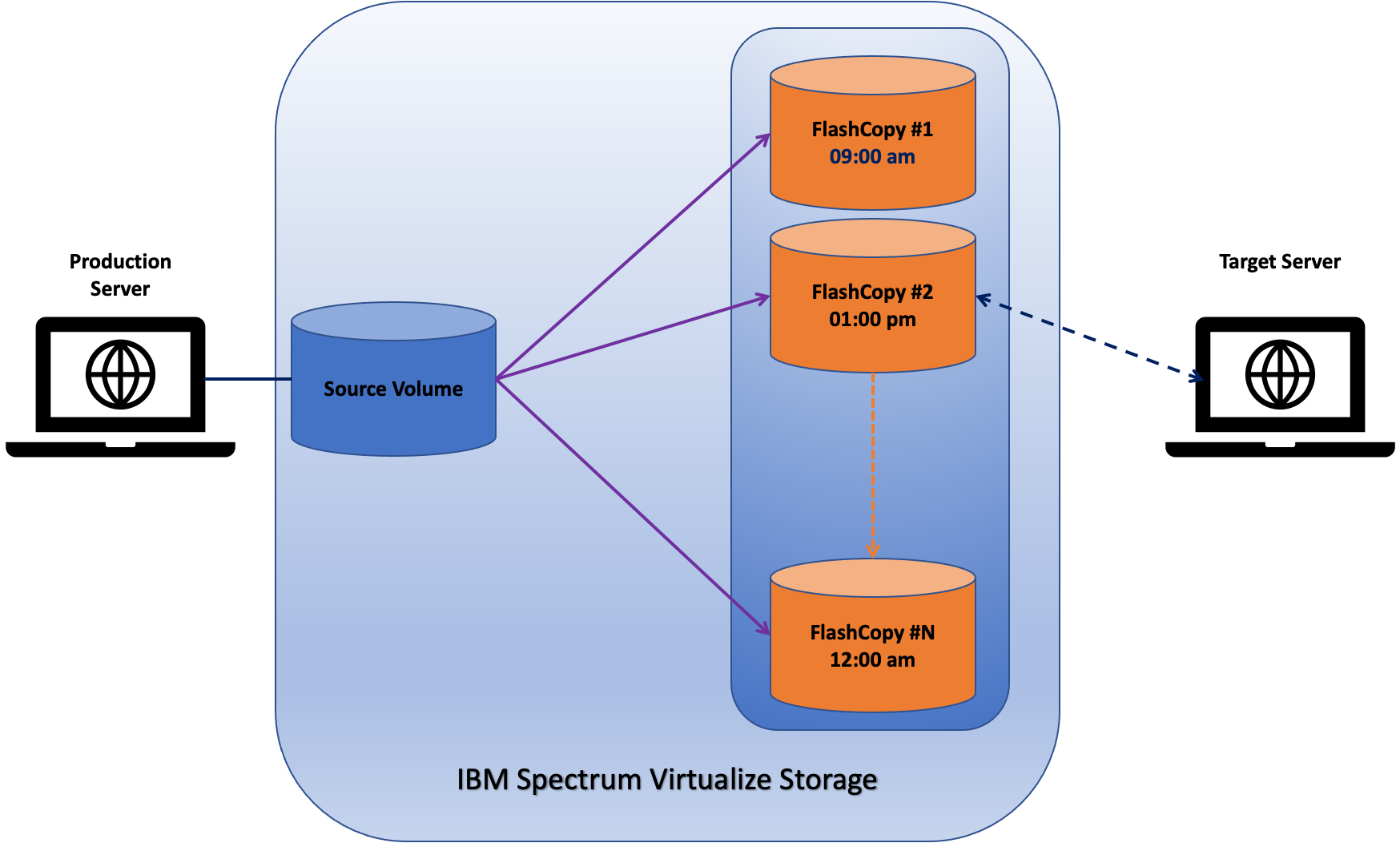
FlashCopy
IBM Spectrum Virtualize FlashCopy feature helps the client to take point-in-time copies of the data. These copies can be used to recover data in case of any breach. These copies can also be used to take system backups or any other testing purposes. IBM Spectrum Virtualize can keep up to 256 copies of a single volume. Each FlashCopy occupies a fraction of the storage capacity by storing only changed blocks of data since last point-in-time copy. These copies can be thin provisioned or compressed to save capacity further.
FlashCopies are online and in-system copies. FlashCopies can be taken at multiple time intervals during the day, without impacting production systems. Later, data can be restored from any of the point-in-time FlashCopies. This restoration happens within the storage system, much faster than traditional tape-based restores. Overall, this allows smaller recovery time objective (RTO) targets to recover from security breaches.
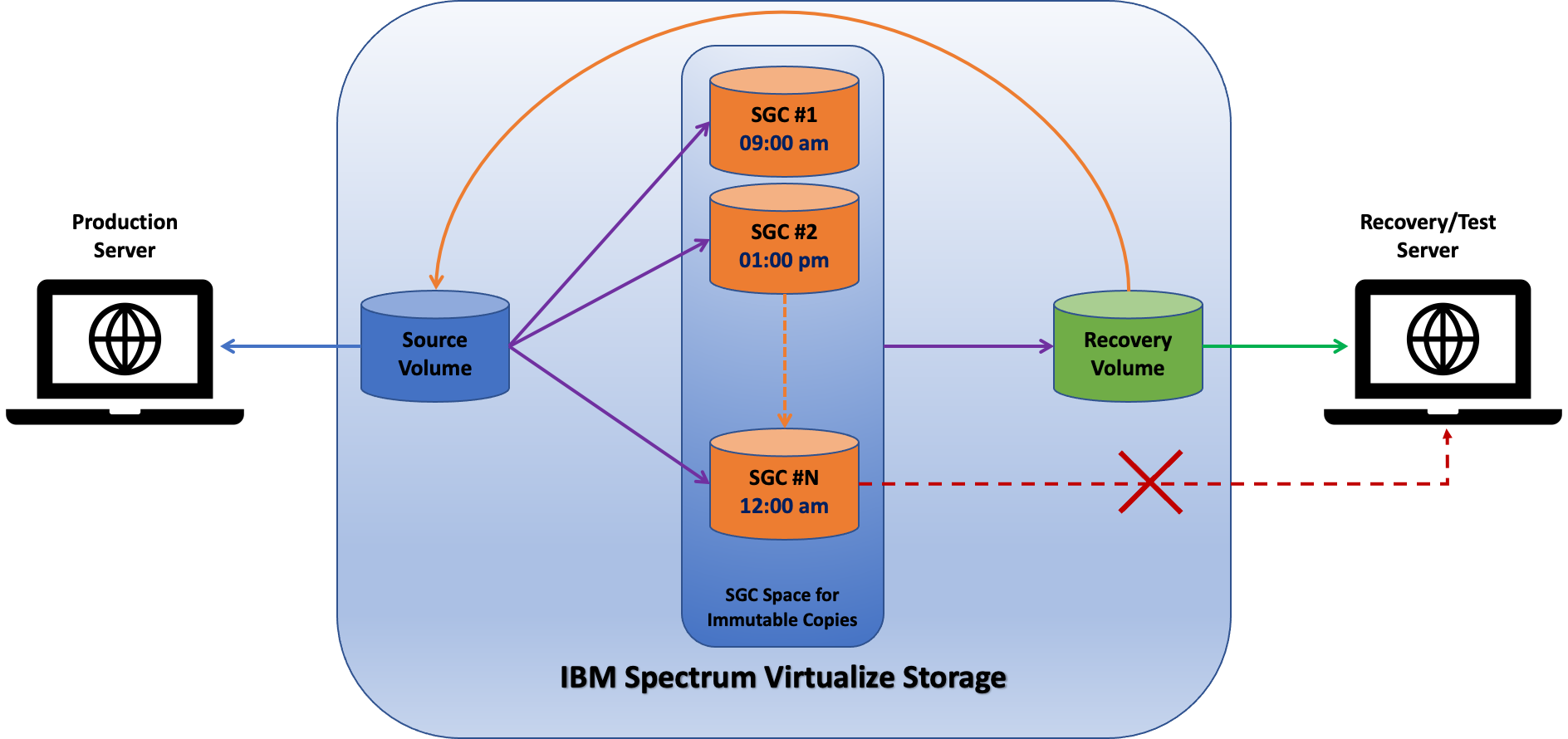
Safeguarded Copy (SGC)
IBM Safeguarded Copy provides the needed additional CR (Cyber Resiliency) layers of protection: immutability and isolation (logical). SGC allows for multiple immutable copies of the data. These immutable copies are retained for a user-specified time period. The immutable copies cannot be deleted unless defined expiration period is complete. If required, an image of immutable copy can be connected to host, but the immutable copy itself cannot be modified or accessed.
In case of any security breach, a user can restore data from SGC to a recovery volume where data sanity checks can be performed. Once a data sanity check is passed, data can be restored on a recovery volume or on a production volume. While restoring data on a production volume, SGC/FlashCopy restores only changed blocks. This enables it to achieve much faster restoration compared to other backup restore process. Data on the safeguarded copy can also be used for forensics and regular data validation purposes.
The IBM Safeguarded Copy solution uses IBM Copy Services Manger as an orchestration tool; CSM provides the automation of SGC creation and expiration.
Cyber Vault
Cyber Vault is an IBM conceptual framework for cyber resiliency (shown below). Cyber Vault is a Systems Lab Services offering to expedite the implementation of the Cyber Vault framework, which is based upon the IBM Safeguarded Copy Solution.
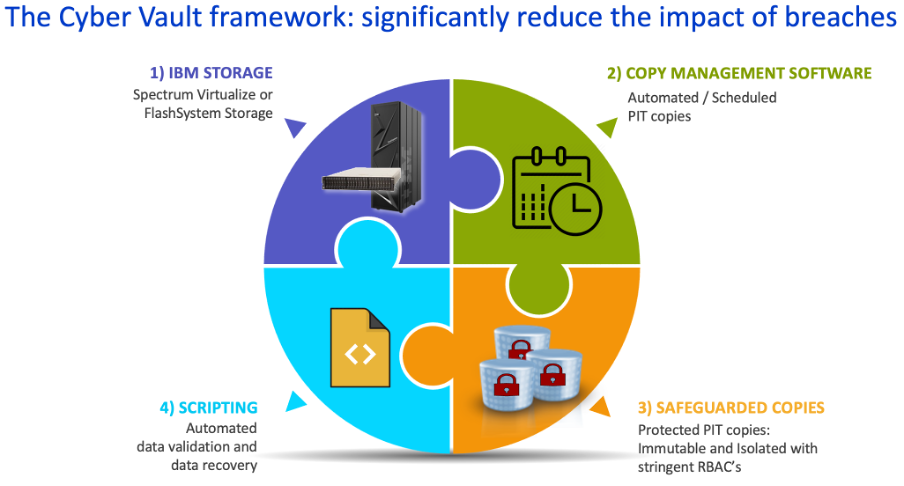
An IBM storage platform (1) that supports Safeguarded Copy (SGC) is required. The Copy Management Software (2) and Safeguarded Copies (3) are underlying components of the SGC solution.
So how does CyberVault differ from Safeguarded Copy (SGC)? It differs by the fourth piece, the automation of data validation and data recovery (4). Cyber Vault’s value proposition is heavily focused on reducing the impact time of a ransomware event, and the scripting piece is paramount to that objective.
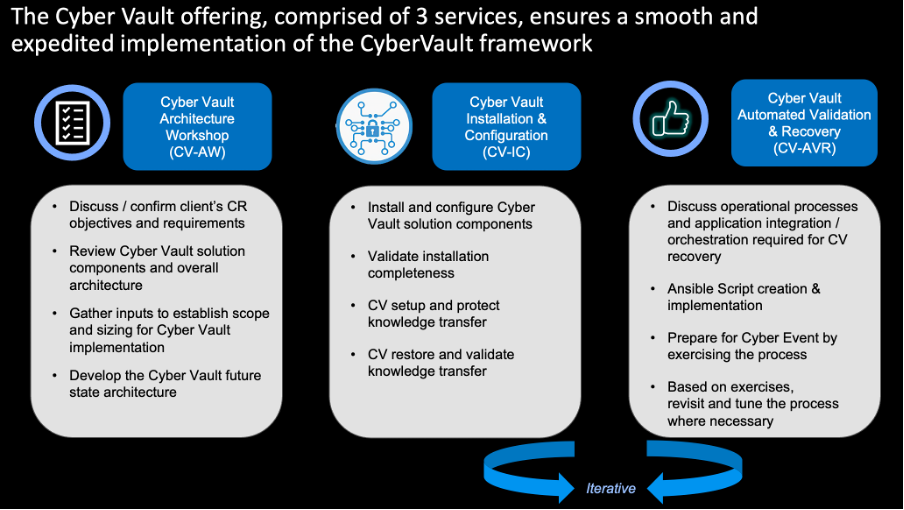
The Cyber Vault offering from Systems Lab Services is comprised of three services (shown below). It begins with the CV-AW. The CV-AW aides in formulating the future state SGC architecture and estimating the additional storage required. In addition, it primes and prepares for the CV-IC and CV-AVR if there is interest in these follow-on services.
In conclusion, IBM Spectrum Virtualize storage offers these enterprise-class cyber security and cyber resiliency features. Multiple features can be used together to provide a comprehensive defense mechanism for modern workloads. Together, these features help the client create a more secure environment to store mission-critical data and prepare for any unforeseen cyber security issues.
Contact us for questions or support
Additional information about IBM FlashSystem can be found in the IBM Documentation link. To learn more about IBM Storage offerings and solutions support, reach out to the Lab Services Storage team. The Lab Services Storage team has helped clients around the world efficiently capture, deliver, manage and protect data with superior performance.