We have updated infomap mapping rule to retrieve EMAIL or Telephone number from LDAP based on delivery Type. It worked !!!
----------------------------------------------------------------------------------------------------------------------------------------
importClass(Packages.com.tivoli.am.fim.trustserver.sts.utilities.IDMappingExtUtils);
importClass(Packages.com.ibm.security.access.user.UserLookupHelper);
importClass(Packages.com.ibm.security.access.user.User);
var username = context.get(Scope.REQUEST, "urn:ibm:security:asf:request:parameter", "myuid");
var deliveryType = context.get(Scope.REQUEST, "urn:ibm:security:asf:request:parameter", "medium");
var hlpr1 = new UserLookupHelper();
// To use the ISAM Runtime configuration use:
// hlpr.init(false);
// added admin credentials to the [bind-credentials] stanza of the
// ldap.conf under the ISAM runtime. ldap.conf file
hlpr1.init(false);
if (username != null) {
IDMappingExtUtils.traceString("Delivery Type from request: " + username);
// put into authsvc context for next mechanism
context.set(Scope.SESSION, "urn:myns", "username", username);
user1 = hlpr1.getUser(username);
if (deliveryType != null) {
IDMappingExtUtils.traceString("Delivery Type from request: " + deliveryType);
// put into authsvc context for next mechanism
context.set(Scope.SESSION, "urn:myns", "deliveryType", deliveryType);
var deliveryAttribute = "admin@localhost";
if (deliveryType == "Email") {
deliveryAttribute = user1.getAttribute("mail");
IDMappingExtUtils.traceString("OTP Delivery medium is Email : " + deliveryAttribute);
}
if (deliveryType == "SMS") {
deliveryAttribute = user1.getAttribute("telephoneNumber");
IDMappingExtUtils.traceString("OTP Delivery medium is SMS : " + deliveryAttribute);
}
// put into authsvc context for next mechanism
context.set(Scope.SESSION, "urn:myns", "deliveryAttribute", deliveryAttribute);
}
success.setValue(true);
}else {
success.setValue(false);
}
------------------------------
Anji Babu
------------------------------
Original Message:
Sent: Tue June 14, 2022 02:17 PM
From: Shane Weeden
Subject: MAC OTP Authentication - REST API call
Excellent. Sounds like you are making progress!
------------------------------
Shane Weeden
IBM
Original Message:
Sent: Tue June 14, 2022 01:18 PM
From: Anji Babu
Subject: MAC OTP Authentication - REST API call
never mind. mapping rule code updated and it worked
------------------------------
Anji Babu
Original Message:
Sent: Tue June 14, 2022 12:55 PM
From: Anji Babu
Subject: MAC OTP Authentication - REST API call
Thank you Shane for the input.
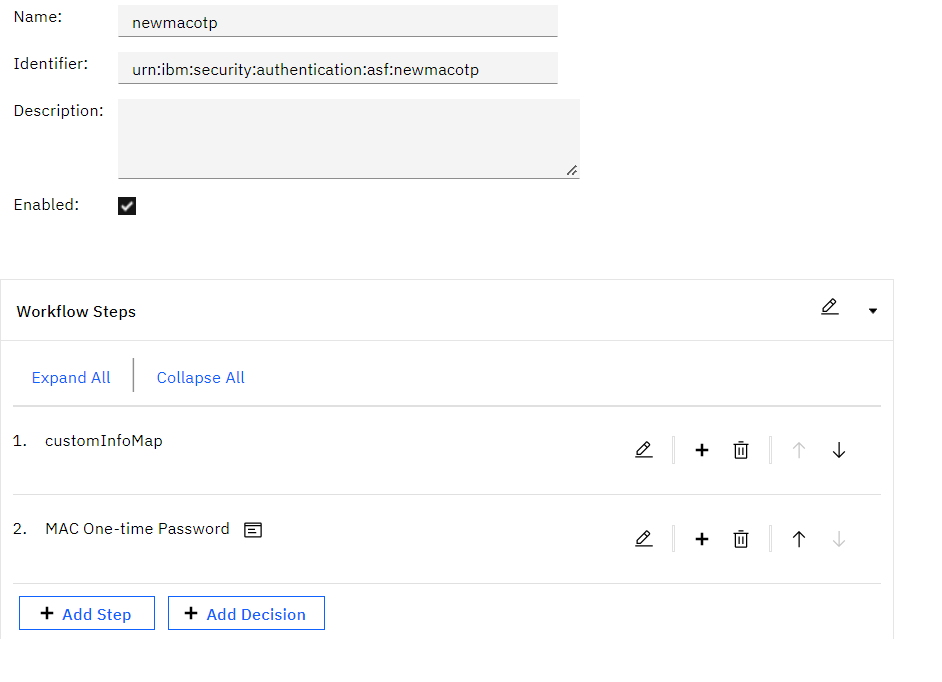
Based on your input, we have updated newmacotp policy with CustomInfoMap and MAC OTP authentication Policies
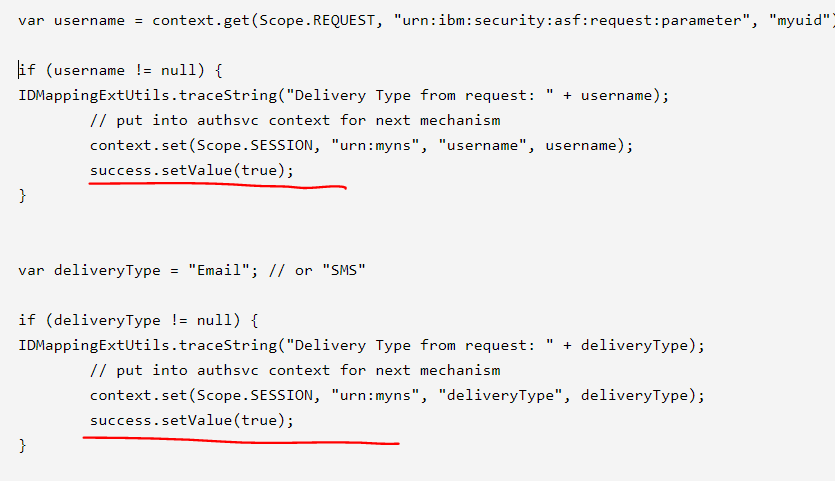
we have hard coded the values in infomap mapping rule, as mentioned below
--->Infomap mapping rule (we have removed the email. it is hard coded for now. later will used userhelp class to pull out from ldap)
importClass(Packages.com.tivoli.am.fim.trustserver.sts.utilities.IDMappingExtUtils);
var username = context.get(Scope.REQUEST, "urn:ibm:security:asf:request:parameter", "myuid");
IDMappingExtUtils.traceString("username from request: " + username);
var deliveryType = "Email"; // or "SMS"
IDMappingExtUtils.traceString("Delivery Type from request: " + deliveryType);
var deliveryAttribute = "testemail"; // "or a formatted phone number"
IDMappingExtUtils.traceString("Delivery Type from request: " + deliveryAttribute);
context.set(Scope.SESSION, "urn:myns", "deliveryType", deliveryType);
context.set(Scope.SESSION, "urn:myns", "deliveryAttribute", deliveryAttribute);
context.set(Scope.SESSION, "urn:myns", "username", username);
when we call newmacotp policy, noticed MAC OTP policy is not invoking. Please see result below. OTP not delivered
curl -k -v -X POST -H "Content-Type:application/json" -H "Accept: application/json" --data "{'myuid':'testuser1'}" "https://isamrp/mga/sps/apiauthsvc?PolicyId=urn:ibm:security:authentication:asf:newmacotp"
output:
{"exceptionMsg":"","location":"/mga/sps/apiauthsvc?StateId=kZh0MSfhtJ38nDUjflw7d9043r39mOlwabOPPVFHzplwYMxQUbUK7izNqMRQioclDDMWsMAOTzhlal0WIjJsgpaU031k7ySmtxjKWPAzFBGjJLSJ2SxxhWBrjhuOwUwA","state":"kZh0MSfhtJ38nDUjflw7d9043r39mOlwabOPPVFHzplwYMxQUbUK7izNqMRQioclDDMWsMAOTzhlal0WIjJsgpaU031k7ySmtxjKWPAzFBGjJLSJ2SxxhWBrjhuOwUwA","message":"","mechanism":"urn:ibm:security:authentication:asf:mechanism:urn:ibm:security:authentication:asf:mechanism:customInfoMap"}
------------------------------
Anji Babu
Original Message:
Sent: Tue June 14, 2022 10:54 AM
From: Shane Weeden
Subject: MAC OTP Authentication - REST API call
Ok, that's fine. Here's what I would do.
I noticed you have your own policy - newmacotp, which is good. This should be a policy that has the following two mechanisms:
Your custom Infomap
Mac One-time password
In the mapping rule for Your custom Infomap, you read in the username via:
let username = context.get(Scope.REQUEST, "urn:ibm:security:asf:request:parameter", "myuid");
You can then use UserLookupHelper or whatever other methods you want to discover email address or phone number and what type of OTP you are going to do (i.e. email or SMS). Put these into the AAC SESSION as attributes like this:
let deliveryType = "Email"; // or "SMS"
let deliveryAttribute = "testuser@mailinator.com"; // "or a formatted phone number"
context.set(Scope.SESSION, "urn:myns", "deliveryType", deliveryType);
context.set(Scope.SESSION, "urn:myns", "deliveryAttribute", deliveryAttribute);
context.set(Scope.SESSION, "urn:myns", "username", username);
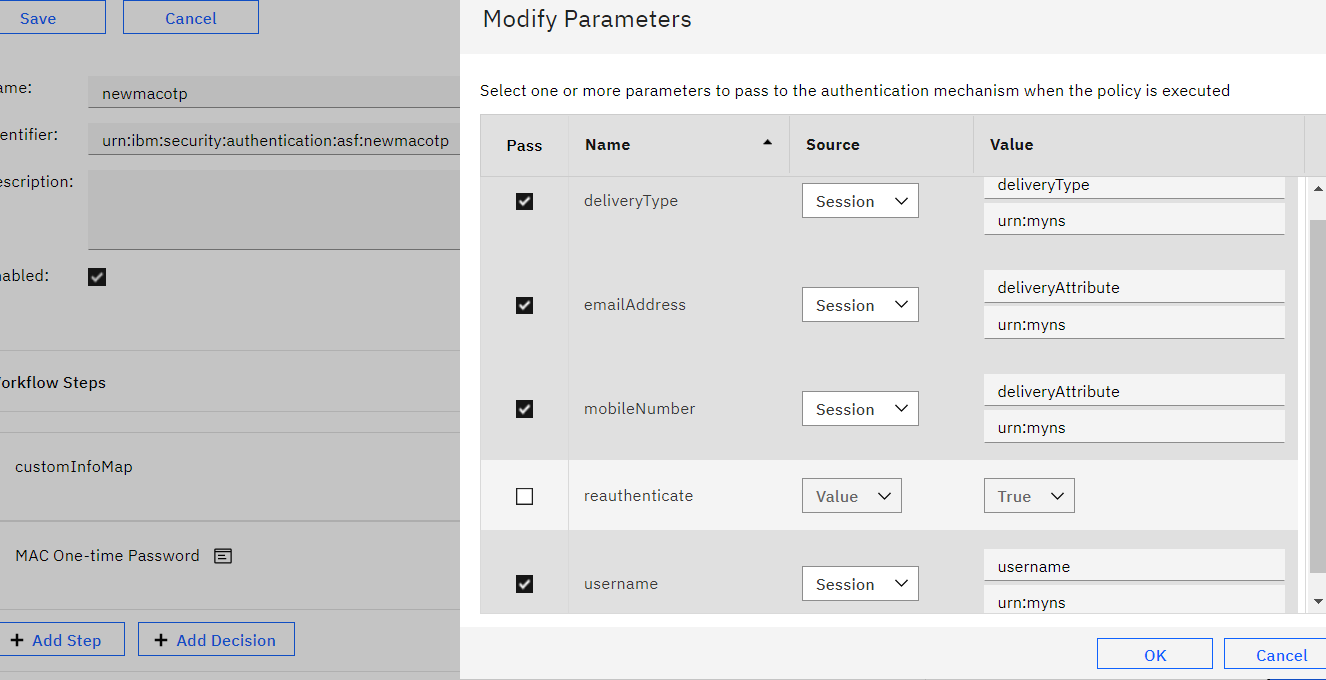
Then in the Mac One Time Password mechanism in the policy, configure the properties like this:
------------------------------
Shane Weeden
IBM
Original Message:
Sent: Tue June 14, 2022 09:59 AM
From: Anji Babu
Subject: MAC OTP Authentication - REST API call
Shane,
we are calling policy programmatically. Below the curl format.
curl --location --request POST 'https://isvarp/mga/sps/apiauthsvc?PolicyId=urn:ibm:security:authentication:asf:newmacotp' \
--header 'Content-Type: application/json' \
--header 'Accept: application/json' \
--data-raw '{'\''myuid'\'':'\''testuser'\''}'
Thank you
------------------------------
Anji Babu
Original Message:
Sent: Tue June 14, 2022 01:29 AM
From: Shane Weeden
Subject: MAC OTP Authentication - REST API call
I'd like to zoom out a bit and verify something. Why are you passing username via a request parameter? Perhaps ok if using apiauthsvc to call the policy programmaticly but if this is a browser accessed policy you have an open spammer. Can you confirm the use case with more detail?
------------------------------
Shane Weeden
IBM
Original Message:
Sent: Mon June 13, 2022 11:42 PM
From: Anji Babu
Subject: MAC OTP Authentication - REST API call
We have configured the Authentication policy with MAC OTP workflow with username request parameter. We are trying retrieve the email from LDAP with the request parameter, USERNAME inside the OTPGetMethods mapping Rules.
We have tried using credential attribute & using user lookup helper class and had no luck with it. any suggestions, please?
------------------------------
Anji Babu
------------------------------