Operationalizing the MITRE Att&ck Framework for Security Operations and Incident Response
Cyber attackers are constantly becoming harder to detect and defend while Security Operations teams such as SOCs, CERTs, and CSIRTs continue to only scratch the surface adapting to these threats. Regardless of organizational size or industry, the evidence is fairly strong that most organizations are pretty bad at security operations.
The number of high-profile breaches are increasing, and organizations – despite high budgets for security - are not adequately able to detect and respond to breaches today. It doesn’t take a genius to figure out that there must be vital gaps in the defensive ecosystem of organizations. Security teams either do not know or are not ready to accept that fact. Identifying these gaps and taking the correct course of action can be the first step towards better security operations.
The MITRE Att&ck framework is the long-awaited answer to these kinds of challenges.
Until now, the cybersecurity industry lacked a holistic approach to detection and mitigation of advanced targeted attacks. In order to develop a holistic approach and make it available to the public, MITRE, a US-based nonprofit organization, spent many years analyzing the global high-profile breaches and categorized them into individual Tactics, Techniques and Procedures (TTPs). As a result, three matrices have evolved: the Pre-Att&ck Matrix, the Att&ck Matrix for Enterprise, and the Att&ck Matrix for Mobile.
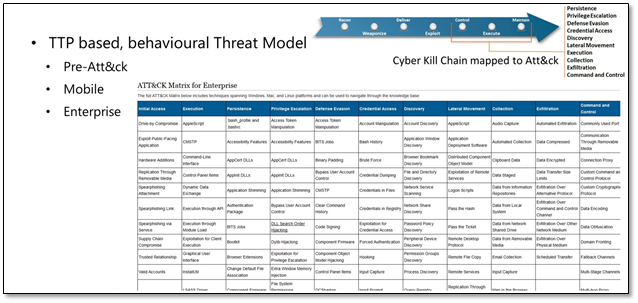
The 11 tactics of the Att&ck Matrix for Enterprise are individual techniques, from “Initial Access” to “Command and Control.” Every technique describes adversarial procedures and methods. The top-right corner shows how the Att&ck Matrix for Enterprise maps to the Cyber Kill Chain. It fits into the last three phases and therefore is a post-compromise matrix. There is also a Pre-Att&ck Matrix available that maps to the pre-compromise phases of the Cyber Kill Chain.
The MITRE Att&ck framework is a TTP-based, behavioral threat model. The goal is to detect and mitigate adversarial behaviors based on the individual TTPs as opposed to Indicators of Compromise-based detection and mitigation. While behaviors of an attack scenario haven’t changed entirely, Indicators of Compromise (IOCs) are changing rapidly, therefore the MITRE Att&ck is entirely concentrated on detection behaviors.
However, it is crucial to have excellent and robust cyber threat intelligence (CTI) in place for starting analysis out on the right foot. This provides real context and informs an organization which Att&ck tactics and techniques to focus on. An example of this is in the screenshot below, which is leveraging CTI from Recorded Future.
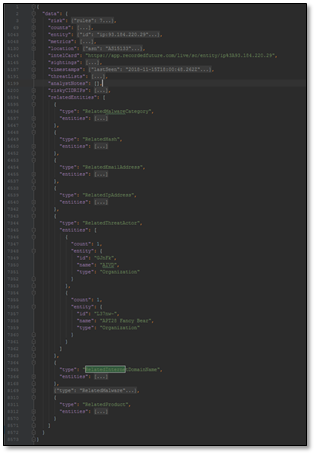
This CTI gathered in the screenshot above is related to an IP address entity of the value 93.184.220.29. The term entity is equivalent to the term “indicator” which means that this is the IOC we are starting our investigation with.
The CTI also has related multiple entities to this indicator in the form of hashes, related email addresses, and related IP addresses. Most importantly, it has discovered a related Threat Actor – “APT 28”, a well-known Russian Threat Group. This specific CTI is actionable based on the context provided.
Based on the provided Threat Actor the next step is to map the CTI to the MITRE Att&ck Matrix. In this example there were two related Threat Actors, namely “AIVD” and “APT 28”. Since MITRE is providing known Threat Actors and the TTPs that they use as part of the Att&ck framework, the TTPs can simply be mapped out based on the Threat Actor name.
Using the free tool from MITRE, the Att&ck Navigator, we can create a visualization of all the TTPs of the selected Threat Actor based on one of the three Att&ck matrices. In this example, the Att&ck Matrix for Enterprise was loaded. Since the CTI provided “APT 28” as a related Threat Actor and this specific Threat Actor is available in the Att&ck framework, the Att&ck Navigator highlights all of TTPs being used by this group.
This process allows analysts to learn how the Threat Group is operating. By right-clicking on a TTP it provides a view of the corresponding technique details. From there, a new browser tab is opened which is linked back to the MITRE website.
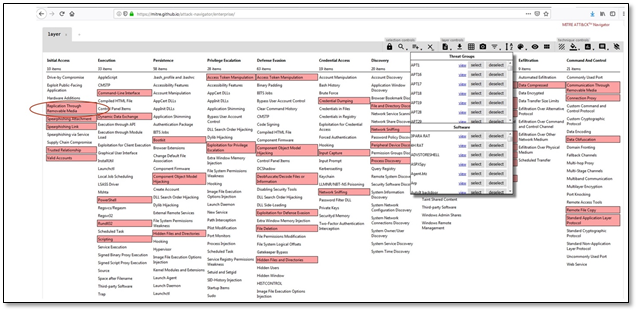
Source: https://mitre.github.io/attack-navigator/enterprise
A TTP on the MITRE website has a unique id (T1091), as seen below. It also provides some high-level information on the corresponding procedures and methods, examples in the wild, detection and mitigation advice, and a vast table of detailed references to known global high-profile breach reports. This is the human readable version of the Att&ck framework.
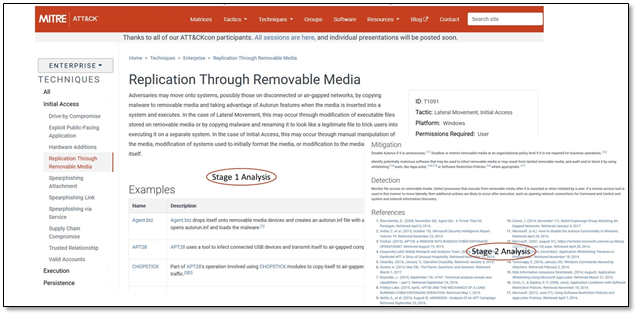
TTP provided information can be divided into two stages: Stage 1 Analysis and Stage 2 Analysis. In contrast to the human-readable version of the Att&ck Matrix, the entire framework is available in machine code, more precisely in STIX2 format. STIX is a useful language that can describe a threat or incident by breaking down its components into objects and provide relationship information between those objects.
A future blog on the MITRE framework will highlight the visualization of related objects in the STIX2 format, and how the enrichment of artifacts in the Resilient platform can be automated to provide more context.
Operationalizing the MITRE Att&ck framework for security operations requires robust CTI and context provided by the MITRE matrices. With information from this framework, action can be taken on attacks using security tools like IBM’s QRadar and Resilient together to form a holistic approach to incident response. The next blog will describe how security analysts can use the MITRE Att&ck framework within these platforms.