iOS device management has grown by leaps and bounds over the last few years. Apple seems to be taking user feedback more seriously and implementing features that both frustrate (deprecating strict features from non-supervised devices) and delight (non-DEP to DEP conversion) admins across the world. One of the more useful features that iOS supports, that gets little lip-service compared to other features, is their shared device solution. As of our 10.80 release, MaaS360 extends our shared device support from Apple School Manager only, to Apple Business Manager devices as well.
So, let's get started.....
Prerequisites
Apple shared devices require some setup in both the Apple Business Manager (ABM) portal, as well as in MaaS360. It's also not going to be supported across all devices, it's limited to iPads only, and specific storage and model minimums must be met.
From the Apple website:
Devices must have at least 32 GB of storage and be supervised. Shared iPad is supported on:
Managed Apple IDs are also required - these are created and managed entirely in the ABM portal.
Please refer to Apple documentation for more info.
The managed Apple IDs should be assigned to users in the MaaS360 portal, though this is not an absolute requirement, failing to do so could result in some unintended consequences (such as user profiles not being received - email configurations, for example). Currently, managed Apple IDs need to be manually added in the portal - either on a user-by-user basis, or using our bulk update tool in the user directory (this will work for users syncing from AD/LDAP sources, in addition to MaaS360 local users).
Alternatively, admins may autofill the managed Apple ID field with the users company email address, just be aware that this is a global setting, and users who have created personal IDs with their company email will not be eligible for managed IDs.
Lastly, in the MaaS360 portal, there has to be a streamlined enrollment profile created specifically for shared devices.
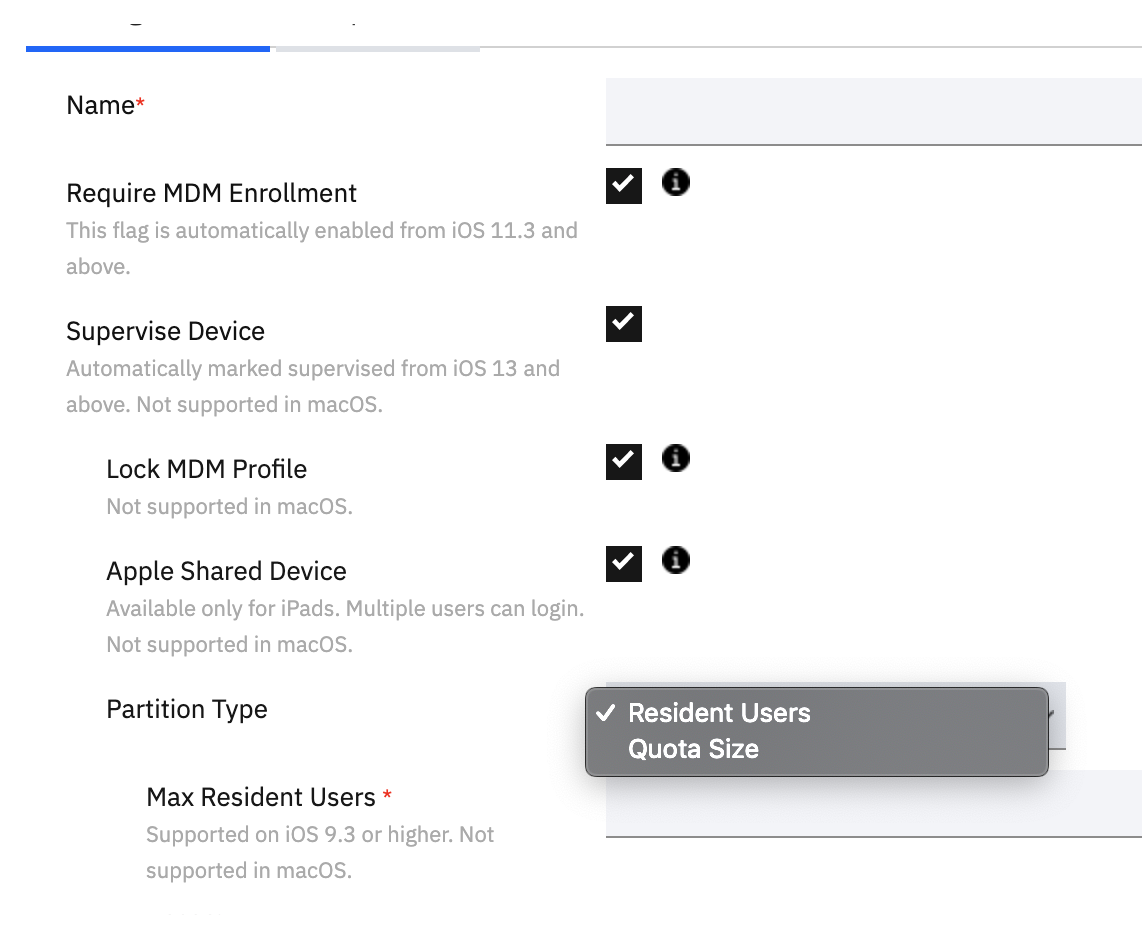
There are a couple of items worth pointing out:
- When the Apple Shared Device option is selected, the "Authenticate User" option disappears. This is because users enrolling shared devices will never authenticate against MaaS360 or our services. The device will not presentt a MaaS360 credential prompt, it will just enroll. Users will then login with their managed Apple ID credentials.
- There are partition types that can be selected to determine how the devices allot space to users.
- Resident Users - Determine the estimated maximum number of users from 2-99. This will not place any caps on user data, however, additional users may be blocked from logging in as storage capacity is reached.
- Quota Size - determine the maximum amount of data allotted to each user (in MB). These caps may not dip below certain minimums that are determined by the amount of device storage. Keep in mind that system and app storage is a shared space that should be removed from the total amount of device storage when determining the limits. From Apple:
-
Devices with a storage capacity of 32 GB: 10 GB for the system, 8 GB for apps and media. The remaining storage is divided among the number of defined users, with 1 GB minimum per user.
Note: Photos won’t sync with a managed Apple ID account for quotas of 1 GB. Only use 1 GB as a minimum when necessary.
-
Devices with a storage capacity 64 GB or greater: 10 GB for the system, 16 GB for apps and media. The remaining storage is divided among the number of defined users, with 2 GB minimum per user.
Here is a sample of the amount of storage capacity that could be allotted to each user (System and Apps and Media partition sizes are static):
Now that the basics are laid out, let's take a look at......
Enrollment & User ExperienceThe device should be assigned the appropriate DEP profile and in a factory reset or out-of-box state. Boot it up, select your language, and connect to your network. The device will mostly take over from here.
Scenario 2 - If the managed Apple ID is associated with a user in the MaaS360 portal, then the device will automatically become assigned to said user, and remain associated until they log out, at which point it will revert to it's original unassigned state. This can be applied retroactively - if a user is given a managed Apple ID in the portal after the device is enrolled, the device will become assigned to that user the next time it checks in to the portal.
#Highlights#Highlights-home#MaaS360