Huge thanks to Kumar Anathanarayan for the initial blog, which I just updated.
MaaS360 Application Security enables enterprises to extend the MaaS360 container capabilities onto enterprise and third party applications, providing operational and security management for iOS and Android applications. Key features include:
- Data Leak Prevention (DLP) controls: Restrict clipboard operations (cut/copy/paste), restrict document export
- Single Sign On (SSO) access: Enforces same container PIN / passcode on all applications within the MaaS360 container. MaaS360 Mobile Enterprise Gateway (MEG) single-sign capabilities that support seamless user authentication to internal apps
- Encryption Support: Encrypt content created by enterprise apps
- App Tunneling: Proxies traffic from apps back to your internal corporate network via the MaaS360 Mobile Enterprise Gateway (MEG)
- App Configuration: Ability to push settings to configure apps - like configuring the server URL for a chat application for e.g.
- Compliance Enforcement: Takes actions on apps when the device is not in compliance with corporate policies.
This blogs walks you through the approach for implementing your application security using MaaS360:
Step 1: Understanding Mobile app types - public vs. private apps, native vs. hybrid
Before you decide to secure your mobile apps, it is important to understand the different types of apps out there. This section clarifies these differences:
A) Public vs. Private apps:
- Public apps are apps that are released to respective market stores - iTunes App Store for iOS and Google Play for Android. Typically meant for public consumption
- Private apps are apps developed specifically for enterprises. These apps are only deployed to employees within the organization and does not typically feature in the public stores. Either enterprises or vendors develop these applications for enterprise-specific use-cases. Private apps are generally referred to as Enterprise Apps.
B) Native vs. Hybrid apps:
- Native apps are
- Apps developed specifically for a mobile OS platform using supported programming languages like Swift / Objective-C for iOS and Java for Android.
- Given that the application is developed using the guidelines for app development for a specific platform and uses native API's that the OS offers, the application would have easy access to built-in device capabilities like accessing Camera, Bluetooth, GPS etc.
- The native apps are faster from a performance standpoint, provides native look and feel to the end user and offers better security.
- However, the time to market these apps are longer since the apps need to be developed using API's for each platform.
- Hybrid apps are
- Web Apps developed in HTML5 and Javascript that are essentially websites bundled into a native wrapper. Built to run across platforms - in this case both iOS and Android
- Looks like native apps but all the data is fed from application servers. The apps make Web Service API calls to fetch this data.
- Built using App development platforms like IBM Worklight, Cordova, Angular, Ionic etc. that provide the native wrapper to these apps
- Faster to market, but suffer on performance since all data needs to be fueled by application servers
Why are these important? Implementing app security varies for different app types. This will be clarified in the blog, so please read on
Step 2: Understanding MaaS360 Application Security Implementation Modes
MaaS360 Application Security can be implemented in two different ways - App Wrapping and App SDK Integration.
A) App Wrapping:
App Wrapping involves unwrapping the app, injecting MaaS360 container security code and re-wrapping the entire package. This process is automatically done by MaaS360 when the app is uploaded to the MaaS360 portal and the administrator has selected the App Wrapping option.
In order to re-wrap your application after injecting MaaS360 container security code, MaaS360 will need the platform specific artifacts for packaging and signing apps. These include:
- iOS Provisioning profile, Code Signing certificate and credentials for iOS
- Keystore file, Keystore Alias Name and credentials for Android
Due to this requirement, App Wrapping is only possible with Enterprise and native Apps. Public Apps cannot be wrapped not because they cannot be, but because the app developer will not share code signing certificates and credentials to re-wrap their app.
The App Wrapping process is outlined below:
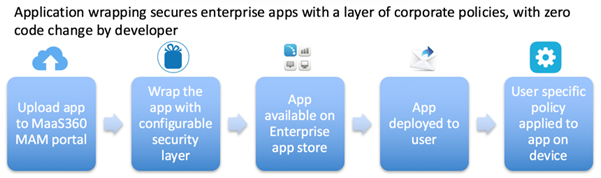
Highlights:
- MaaS360 adds security layer to enterprise apps (iOS and Android) by injecting code and re-wrapping the apps.
- Requires no code changes to be made by developers. Security layer is automatically added by MaaS360 on-demand
- Requires code signing certificates, keystore credentials etc. to re-sign the app after code injection
- Supports private / enterprise only. Supports both native and hybrid apps.
B) App SDK Integration:
App SDK Integration involves including the MaaS360 App Security Software Development Kit (SDK) during the app development process itself. This provides greater flexibility and fine grained control over how the App security features can be leveraged in your application. App SDK Integration provides the same set of feature of App Wrapping and much more.
The App SDK Integration process is outlined below:
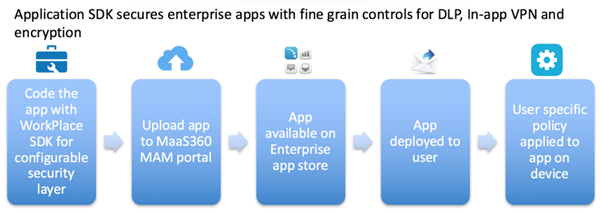
Highlights:
- Requires Application developers to integrate the MaaS360 App Security SDK during the app development lifecycle
- Offers granular controls over security feature integration
- Offers additional API’s to fetch MaaS360 user and device data for applications to use (username, device information etc.)
- Supports both native and hybrid apps
Step 3: What mode should I choose for my enterprise apps?
One of the most common question that I get asked is - what should I choose for my apps? Should I wrap them with MaaS360, or ask our developers to integrate with the MaaS360 SDK or just not wrap at all? What are the benefits of each approach?
The answer to this depends on what type of apps you have and the requirements for your use-cases. Here are some guidelines:
- No Wrapping / SDK, just MDM managed apps:
- If the app you want to deploy has no confidential data and you are not concerned about any data leak, you don't really have to wrap or build with the SDK. You can just push the app to the device from MaaS360. MaaS360 provides the following security mechanisms via MDM:
- Ability to remotely uninstall the app
- Ability to automatically uninstall the app if the device is out of compliance - like Jailbroken / rooted, not adhering to passcode policies, or any other corporate policy per-say.
- You can prevent app backups or enforce encrypted backups of app data, enforce managed status of apps on iOS, and only restrict data exports from your app to other managed apps only (pushed and managed via MDM) in iOS etc.
- If your app can be managed with these controls, you really do not need any app wrapping / SDK for your apps
- App Wrapping:
- You would use app wrapping if you have the following scenarios:
- Your app has confidential data and you need to protect this data on the app from data leak. You also want to enforce encryption of your app data locally on the device.
- Your app needs to contact an internal resource on your corporate network that is not exposed to the internet. The app with the help of MaaS360 wrapper and Mobile Enterprise Gateway can get the app to talk to your internal server.
- You need MaaS360 to help configure your application by passing in app configuration parameters like username, server URL, email address etc.
- Restrict usage of app when the device is not in compliance with your corporate policies - and removal of the app is not an option (like MDM managed apps use-case above)
- Enforce the same container password / PIN to unlock all wrapped apps
- App SDK:
- App SDK provides the same set of functionality as App Wrapping for the most part and few things beyond. Here are some scenarios where SDK would be better suited for your use-case (in addition to App Wrapping use-case)
- Extract information like username, domain and email of the user from the MaaS360 app
- Implement callbacks for security events like device compliance events and handle your app data in a customized way
- Ability to send email from your app via MaaS360 Secure Mail
- Ability to open a link from your app via MaaS360 Secure Browser
- Ability to open a document from your app via MaaS360 Secure Viewer / Editor
The following tables provides more details on all these capabilities.
Table 1: Device and user identity and access
|
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
Get user and device information
|
Allows the SDK to obtain information about the device and user that includes Device UDID, MaaS360 Device ID, User name, Access Groups, Email Address, Compliance Status, and Out of Compliance reasons (if applicable).
|
Provides unique identification details about the user and the device.
|
Yes
|
Yes
|
Yes
|
Yes
|
N/A
|
N/A
|
|
Single sign-on. Access control across apps
|
Allows the user to use a single PIN to access any app that is built by the same developer.
|
Users sign on with a simple container PIN and stay logged in until the login time lapses.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
User custom attribute support
|
Allows custom user-level attributes to be defined and propagated to the app.
|
Enterprises define custom attributes for users that are used across apps.
|
Yes
(Note A )
|
Yes
(Note A )
|
Yes
|
Yes
|
|
|
|
Shared device support
|
Allows the user to access the app only when the user is signed in, and prevents the user from accessing the app when the user is signed out.
|
Makes sure that data is secure when multiple users share a single device.
|
Yes
(Note B )
|
Yes
(Note B )
|
Yes
|
Yes
|
|
Yes
|
Table 2: Security and Compliance
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
Compliance enforcement
|
Sets up policies for user and device compliance and enforces restrictions on apps for non-compliant devices.
|
Detects user and device compliance events and automatically enforces restrictions on apps, such as blocking user access to an app.
|
Yes
|
Yes
|
Yes
|
Yes
(Note C )
|
Yes
(Note D )
|
Yes
|
|
Location and time-based policies
|
Defines location and time boundaries for using an app.
|
Allows or blocks users from accessing an app based on time and location.
|
|
|
Yes
|
Yes
|
|
Yes
|
|
Restrict access on jailbreak
|
Detects jail-broken devices and restricts user access to an app. These APIs are enforced automatically by the app SDK or the SDK provides the delegate call backs on these events for the app to implement.
|
Detects jailbreaks and immediately restricts the user from accessing an app.
|
Yes
|
Yes
|
Yes
|
Yes
(Note C )
|
Yes
|
Yes
|
|
Restrict access after long periods of inactivity
|
These APIs are enforced automatically by the app SDK or the SDK provides the delegate call backs on these events for the app to implement.
|
Enforces authentication to an app after a specified login period expires.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
Restrict access on selective wipe
|
These APIs are enforced automatically by the app SDK or the SDK provides the delegate call backs on these events for the app to implement.
|
Sends an alert when the admin starts a selective wipe to protect or delete corporate data within the app.
|
Yes
|
Yes
|
Yes
|
Yes
(Note C )
|
Yes
|
Yes
|
Table 3: Data protection features
|
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
Data at rest encryption
|
Enforces maximum security for the app data at rest.
|
Encrypts the app data for more security. Encrypts the metadata for the app, the app database, and all the files that are in use for the app.
|
Yes
|
Yes
(Note E )
|
Yes
|
Yes
(Note F )
|
Yes
|
Yes
|
|
Advanced encryption handling
|
Encrypts an app that uses a container PIN.
|
Provides simpler key handling for encryption.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
|
Encrypted inter-app data transfer with MaaS360
|
Encrypts and transfers data between MaaS360 and the app securely without the possibility of man-in-the-middle attacks.
|
Encrypts data while in transit between MaaS360 and the apps on the device.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
|
Restrict cut, copy, or paste
|
Allows cut, copy, or paste only within the set of containerized apps.
|
Restricts the user from copy or pasting documents from within the container to a personal app.
|
Yes
|
Yes
|
Yes
|
Yes
(Note G )
|
Yes
|
Yes
|
|
Restrict screenshot
|
Restricts the user from taking a screen capture of the device.
|
Protects sensitive data from leaking through screen captures.
|
N/A
(Note H )
|
N/A
|
Yes
|
Yes
(Note J )
|
N/A
(Note H )
|
Yes
|
|
Restrict import from camera or gallery
|
Restricts the user from using the camera or importing images from the Gallery into the app.
|
Isolates work apps from personal images and data.
|
|
|
Yes
|
Yes
|
|
Yes
|
|
Restrict import from SD card
|
Restricts the user from importing content from the SD card into the app.
|
Isolates work apps from extraneous content that is stored on the SD card.
|
N/A
|
N/A
|
|
|
|
Yes
|
|
Restrict file import
|
Restricts the importing of files from other apps into the containerized app.
|
Prevents users from importing non-work related documents into the containerized app.
|
|
|
Yes
|
Yes
|
|
Yes
|
|
Filter notifications if container is locked
|
Prohibits notification messages from the app when the container is locked, preventing data leakage.
|
Blocks sensitive notification messages from displaying on the screen if the container is locked. These notifications are displayed when the user unlocks the container.
|
|
|
Yes
|
Yes
|
|
Yes
|
|
Allow file import from set of whitelisted apps
|
Allows the importing of files from a select list of whitelisted apps, as defined in the policy.
|
Allows users to import documents from a select list of trusted apps into the containerized app.
|
|
|
Yes
|
Yes
|
|
|
|
Restrict file export
|
Restricts the exporting of files to allowed apps only.
(The SDK provides a separate interaction controller to handle this action.)
|
Prevents the leakage of files and allows files to be opened in a set of whitelisted and containerized applications. Users cannot export files to other apps.
|
Yes
|
Yes
|
Yes
|
Yes
(Note J )
|
Yes
|
Yes
|
|
Restrict printing
|
Restricts the printing of files, if enabled.
|
Prevents leakage of data from printing. Users cannot print from the wrapped app.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
Certificate pinning
|
Validates that the trusted CA public certificates match with certificates that are pinned by the app.
|
Protects apps from certificates that are fraudulent.
|
|
|
Yes
|
Yes
|
|
Yes
|
Table 4: Enterprise Gateway features
|
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
Per-app VPN
|
Establishes the gateway access for the app to access resources behind the corporate firewall.
|
Provides app-level intranet access without a device-level VPN. Encrypts data in motion. Reduces VPN traffic since only corporate apps fetch data through the gateway, while all personal apps directly access the internet.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
Regional gateway support for per-app VPN
|
Uses a regional MaaS360 gateway for the per-app VPN based on the geographic location of the user.
|
Allows users to access data faster due to reduced network latency.
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
Yes
|
|
Corporate Network Detect
|
Uses direct access and skips the per-app VPN in the corporate network.
|
Allows users to access data faster through direct access to corporate resources while in the corporate network.
|
Yes
|
Yes
|
|
|
Yes
|
Yes
|
|
Identity Certificate for direct gateway
|
Allows Identity Certificate validation by a load balancer during SSL negotiations.
|
Validates an identity certificate from the device by using a direct gateway setup with a load balancer.
|
|
|
Yes
|
Yes
|
|
Yes
|
Table 5: App configurations and app security
|
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
App configuration
|
A configuration file with required inputs is passed from MaaS360 and delivered securely to the app.
|
Provides a better user experience because the app is preconfigured.
|
Yes
|
Yes
|
Yes
|
Yes
|
N/A
|
N/A
|
|
App authenticity
|
Validates the app signature before an app accesses the MaaS360 container.
|
Makes sure that tampered or malicious apps do not gain access to the container.
|
|
|
Yes
|
Yes
|
|
Yes
|
Table 6: Interaction with MaaS360 WorkPlace
|
|
Feature name
|
Feature description
|
Benefit
|
iOS Native SDK
|
iOS Cordova SDK
|
Android Native SDK
|
Android Cordova SDK
|
iOS Wrap **
|
Android Wrap **
|
|
Send MaaS360 email
|
Provides an interaction controller that is used to send email through MaaS360 Secure Mail with or without attachments.
|
Allow users to send email from your app with MaaS360 Secure Mail.
|
Yes
|
Yes
|
Yes
|
Yes
|
N/A
|
N/A
|
|
Open document directly in Secure Viewer
|
Provides the option for developers to open documents directly in the Secure Viewer, since Android does not provide a viewer.
|
Enables developers to easily provide document views within apps that use the MaaS360 SDK.
|
N/A
|
N/A
|
Yes
|
Yes
|
N/A
|
Yes
|
|
Save documents in MaaS360 app
|
Provides an interaction controller for the app to allow users to save the document securely in the MaaS360 app.
|
Users can save documents from any app into the My Docs section of the container.
|
Yes
|
Yes
|
Yes
|
Yes
|
N/A
|
N/A
|
|
Open links in MaaS360 Secure Browser
|
Allows users to open links from apps in the MaaS360 Secure Browser.
|
Users are directed to the MaaS360 Secure Browser to open URLs present in apps, including intranet sites without a device-level VPN.
|
Yes
|
Yes
|
Yes
|
Yes
|
|
|
|
Browse in MaaS360 Docs
|
Provides an interaction controller for the app to allow users to browse documents securely from MaaS360 Docs.
|
User can browse documents in MaaS360 Docs from any app securely.
|
|
|
Yes
|
Yes
|
|
Yes
|
|
Edit documents in MaaS360 Secure Editor
|
Provides an interaction controller for the app to allow users to edit the document securely in the MaaS360 Secure Editor. The SDK handles the transfer of the document to the editor and handles the receiving of the document from the editor when the edit is complete.
|
Allows users to edit a document directly inside the container by using the MaaS360 Secure Editor.
|
Yes
|
Yes
|
Yes
|
Yes
|
|
Yes
|
Table 7: Notes and symbols
|
|
Note
|
Description
|
|
A
|
Can be used with app configuration
|
|
B
|
Requires app reconfiguration
|
|
C
|
Selective Wipe action by MaaS360 app only. No delegate call backs.
|
|
D
|
Only for selective wipe events
|
|
E
|
Provided by iOS. JSON database encrypted by Worklight.
|
|
F
|
Files and text encrypted by MaaS360. JSON database encrypted by Worklight.
|
|
G
|
By extending the MaaS360WLDroidGap class
|
|
H
|
Available by using MDM
|
|
J
|
By extending the MaaS360WLDroidGap class
|
|
N/A
|
Not possible or made available by the OS
|
|
**
|
Wrapping support for iOS Cordova-based apps is at parity with SDK-integrated apps, while wrapping is not currently supported for Android Cordova-based apps.
|
Step 4: More Education
Now that you have an overview of the Application Management Basics with MaaS360 the next step is to check out the course MaaS360: Application Management Tips and Tricks on the Security Learning Academy.
You can find the course here: https://www.securitylearningacademy.com/enrol/index.php?id=1879. You will need to set up an IBM ID to access this course.
There is also th MaaS360 Application Management and Security course, which goes through the practicalities of securing your apps. You will find it here as well: https://www.securitylearningacademy.com/enrol/index.php?id=1879.