· Introduction to LV encryption and current authentication methods:
Logical Volume encryption is AIX feature which got introduced in 2020 primarily on AIX 7.3 TL1. Using this feature, customers can enable encryption on logical volumes which helps to make data more secure and have data in encrypted format. AIX has used different authentication mechanisms to encrypt a logical volume. From AIX 7.3 TL1, we have Passphrase (password), keyserver, PKS (Proportional Keystore Size), keyfile.
Below is the brief update on how these authentication method works :
Passphrase : It is like password authentication method. Passphrase input maximum length is 32 characters. It is then concatenated to a salt value which is 64 bytes long . A wrapping key is derived from the passphrase and this wrapping key is used to encrypt the masterkey which is unique per LV
PKS (Proportional Keystore Size): In this method the wrapper is stored in the PSS opaque Object (Kernel). The PSS APIs will be allowed to access the kernel and they Keys will be identifed by LVIDs. Command line interface hdcryptomgr is designed to handle this authentication method.
Keyfile : In Keyfile method the wrapping key is stored in a plain text file and it will be used to lock and unlock the LV encrypted data. Authenticating with keyfile requires to provide the path to keyfile to use. If the path to keyfile is not provided on command line, it is dynamically requested.
Keyserver : A key server is used to securely store key material. The access to the key server is secured by certificate exchanges between the client and the server. Keyserver connectivity is configured in an ODM table, controlled by the keysvrmgr CLI. Admin is responsible to associate each keyserver to a unique identifier in this ODM table.
In keyserver authentication method, customer need to configure separate keyserver which is called SKLM (Security Key Life Cycle Manager) and they need to make sure they maintain to make sure keys are properly stored. Configuring SKLM is overhead in this keyserver method.
From AIX 7.3 TL1, AIX has introduced another authentication method called HPCS (Hyper Protect Crypto Services) which eliminates additional overhead of configuring keyserver. This authentication method uses IBM cloud instance which already has HPCS feature enabled.
· Working with HPCS authentication (add, verify, rekey, remove)
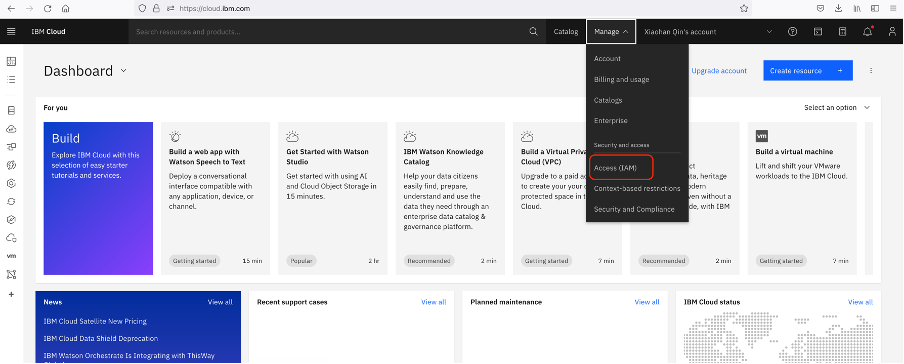
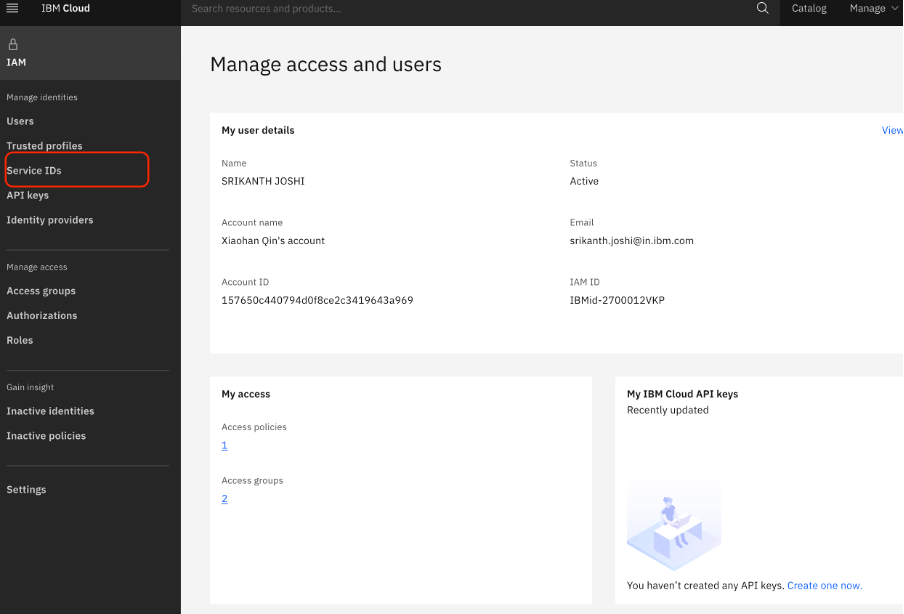
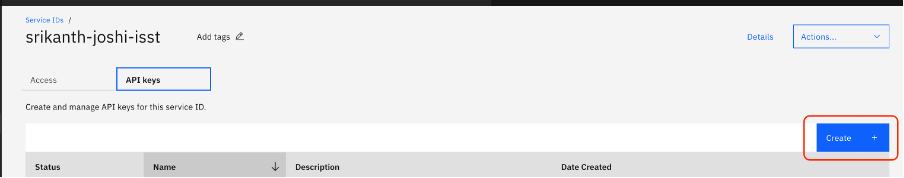
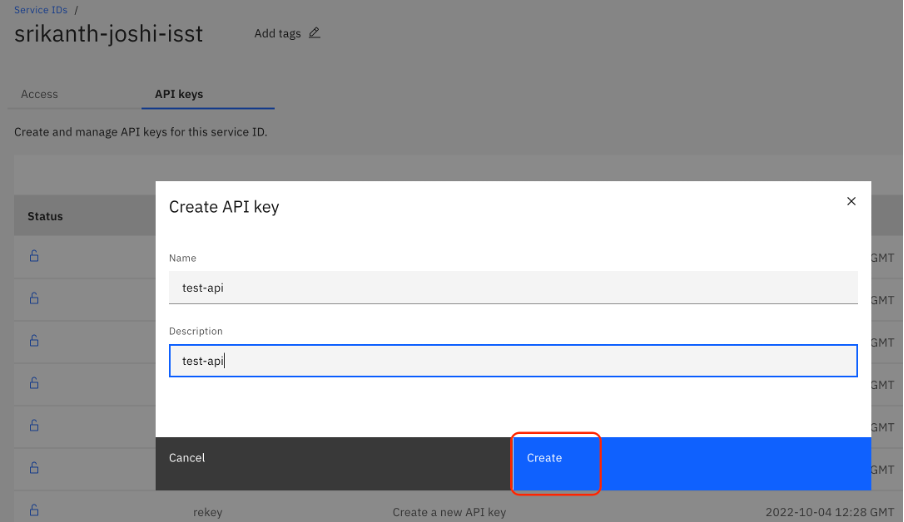
Once HPCS is configured in IBM cloud, we need to generate api-key which is shown below snapshots:

1. Once api-key is generated, we need to use use this api-key to communicate from AIX system to IBM cloud instance. Use below command to add key server to AIX ODM database
# keysvrmgr add -t hpcs -a inst_id=f1a98698-a447-4563-9149-d44494f5cb18 -a api_key=CDwIoxOu-Tdr2-Hj9Tr3ft4i-415Cli7RqKUtZYtdqm3 -a svr_region=https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2 test
HPCS server test successfully added
Please run 'keysvrmgr verify -t hpcs test' to verify the ODM record.
#
Here, we can get inst_id and svr_region from IBM cloud instance UI.
2. Once api-key added to ODM, we need to run verify to make sure your system communicates with HPCS server via the api-key
# keysvrmgr verify -t hpcs test
Start verifying the following ODM record:
Server name: test
Server region: https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2
Instance id: f1a98698-a447-4563-9149-d44494f5cb18
ODM record test passed verification
#
3. We can add another HPCS server with same api-key with different HPCS server name using below command :
# keysvrmgr add -t hpcs -a inst_id=f1a98698-a447-4563-9149-d44494f5cb18 -a api_key=CDwIoxOu-Tdr2-Hj9Tr3ft4i-415Cli7RqKUtZYtdqm3 -a svr_region=https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2 test1
HPCS server test1 successfully added
Please run 'keysvrmgr verify -t hpcs test1' to verify the ODM record.
# keysvrmgr verify -t hpcs test1
Start verifying the following ODM record:
Server name: test1
Server region: https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2
Instance id: f1a98698-a447-4563-9149-d44494f5cb18
ODM record test1 passed verification
#
4. If end user wants to modify svr_region, inst_id or api_key, we can use modify flag
# keysvrmgr modify -t hpcs -h
Usage: keysvrmgr modify [-h] -t <server_type> { -a <attribute>=<value> ... } server_id
For <server_type> = hpcs, the following attributes can be specified:
svr_region: HPCS region URL. An example is:
https://us-east.broker.hs-crypto.cloud.ibm.com/crypto_v2
inst_id : HPCS instance id.
api_key : HPCS API key.
#
5. We can use remove flag to remove HPCS server from AIX ODM
# keysvrmgr show -t hpcs
List of key servers:
SVR_NAME REGION INST_ID
test https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2 f1a98698-a447-4563-9149-d44494f5cb18
test1 https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2 f1a98698-a447-4563-9149-d44494f5cb18
# keysvrmgr remove -t hpcs test1
HPCS server test1 successfully removed
# keysvrmgr show -t hpcs
List of key servers:
SVR_NAME REGION INST_ID
test https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2 f1a98698-a447-4563-9149-d44494f5cb18
#
6. We can check odmget command to check on HPCS server entries in ODM database
# odmget HpcsSvr
HpcsSvr:
svr_name = "test"
svr_region = "https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2"
api_key = "CDwIoxOu-Tdr2-Hj9Tr3ft4i-415Cli7RqKUtZYtdqm3"
inst_id = "f1a98698-a447-4563-9149-d44494f5cb18"
update_time = 1668666370
flags = 0
#
7. We have another option called rekey where we can create api-key from AIX system rather than going to IBM cloud instance. This new api-key will replace the existing api-key in IBM cloud
# keysvrmgr rekey -t hpcs test
Start rekey the following ODM record:
Server name: test
Server region: https://us-south.broker.hs-crypto.cloud.ibm.com/crypto_v2
Instance id: f1a98698-a447-4563-9149-d44494f5cb18
Update succeeded for ODM record test:
Old API_key: CDwIoxOu-Tdr2-Hj9Tr3ft4i-415Cli7RqKUtZYtdqm3
New API_key: rRk8szd0rTN78vXwgaDy8-5edsyWfbctuAs9rWyecJeQ
Rekey succeeded for ODM record test
#
· Hdcryptmgr command enhancement to work on HPCS authentication
Now that we have added HPCS server into AIX ODM, lets see how we can use hdcryptmgr command to do LV encryption using HPCS authentication method.
Assuming we can Volume Group and Logical Volumes created with LV encryption enabled, below are different ways of working on LV encryption via HPCS authentication method
1. We have LV with name “testlv” which is created and have default authentication method passphrase:
# hdcryptmgr showlv -v testlv
NAME CRYPTO_STATUS %ENCRYPTED NOTE
testlv unlocked 100
-- Authentication methods ------------
INDEX TYPE NAME
#0 Passphrase initpwd
#
2. We need to hdcryptmgr authadd -t hpcs to add HPCS method
# hdcryptmgr authadd -t hpcs -m test -n testlv testlv
HPCS authentication method with name "testlv" added successfully.
#
# hdcryptmgr showlv -v testlv
NAME CRYPTO_STATUS %ENCRYPTED NOTE
testlv unlocked 100
-- Authentication methods ------------
INDEX TYPE NAME
#0 Passphrase initpwd
#1 HPCS testlv
#
3. We can give multiple names with same HPCS server:
# hdcryptmgr showlv -v testlv
NAME CRYPTO_STATUS %ENCRYPTED NOTE
testlv unlocked 100
-- Authentication methods ------------
INDEX TYPE NAME
#0 Passphrase initpwd
#1 HPCS testlv
#2 HPCS testlv1
#
4. We can also add via different HPCS server:
# hdcryptmgr showlv -v testlv
NAME CRYPTO_STATUS %ENCRYPTED NOTE
testlv unlocked 100
-- Authentication methods ------------
INDEX TYPE NAME
#0 Passphrase initpwd
#1 HPCS testlv
#2 HPCS testlv1
#3 HPCS srik
#
5. We can use authcheck to see if HPCS authentication is working:
# hdcryptmgr authcheck -t hpcs testlv
-- Authentication methods ------------
INDEX TYPE NAME
#1 HPCS testlv
#2 HPCS testlv1
#3 HPCS srik
Authentication method index to use: 1
HPCS authentication check succeeded.
# hdcryptmgr authcheck -t hpcs testlv
-- Authentication methods ------------
INDEX TYPE NAME
#1 HPCS testlv
#2 HPCS testlv1
#3 HPCS srik
Authentication method index to use: 2
HPCS authentication check succeeded.
# hdcryptmgr authcheck -t hpcs testlv
-- Authentication methods ------------
INDEX TYPE NAME
#1 HPCS testlv
#2 HPCS testlv1
#3 HPCS srik
Authentication method index to use: 3
HPCS authentication check succeeded.
#
6. We can use authdelete if we want to delete any of the HPCS authentication
# hdcryptmgr authdelete -t hpcs testlv
-- Authentication methods ------------
INDEX TYPE NAME
#1 HPCS testlv
#2 HPCS testlv1
#3 HPCS srik
Authentication method index to delete: 1
HPCS authentication check succeeded.
Authentication method (name: "testlv" index: #1) deletion for device testlv succeeded.
#
# hdcryptmgr showlv -v testlv
NAME CRYPTO_STATUS %ENCRYPTED NOTE
testlv unlocked 100
-- Authentication methods ------------
INDEX TYPE NAME
#0 Passphrase initpwd
#2 HPCS testlv1
#3 HPCS srik
#
· Benefits of using HPCS auth method
1. Rekey fails if we do more than 300 rekey operations in a loop. However, customers will usually do rekey once in 3-6 months.
2. Keysvrmgr verify might fail for few of the api-keys if we run in loop. However, it will succeed if we give sleep of 2-5 sec interval within loop.
3. We might see authadd fail due to HPCS performance. If we retry, it will succeed.
· References
1. Basics of encrypted logical volumes - https://www.ibm.com/docs/fr/aix/7.2?topic=system-encrypted-logical-volumes
2. Overview of logical volume manager :
https://www.ibm.com/docs/en/ds8880/8.0?topic=migrating-overview-aix-logical-volume-manager