The IBM MQ Appliance is a hardware offering that provides a dedicated and optimised platform for hosting IBM MQ queue managers. It includes integrated support for high availability (HA), disaster recovery (DR) and IBM MQ Advanced capabilities, such as Advanced Message Security (AMS). You can read more about the appliance at https://www.ibm.com/docs/en/mq-appliance/9.2?topic=overview-introduction-mq-appliance.
The appliance has two types of built-in storage:
- Encrypted flash storage, where the appliance firmware, the system configuration, and system logs reside.
- RAID (SSD) storage, where queue manager data, queue manager logs, and other MQ configuration files reside (equivalent to /var/mqm on Linux and UNIX).
From version 9.2.5, the appliance firmware supports encrypted file systems on the RAID (SSD) storage, which enables all MQ data to be encrypted at REST for compliance with corporate security policy and industry regulation. Encrypting file systems on the SSDs helps to prevent data being exposed if the disks are lost, stolen, or disposed of insecurely. In a HA or DR configuration, encrypted queue manager file systems are replicated in their encrypted state, which provides added protection while the data is in transit over a network. Encryption is implemented in the appliance firmware, so no hardware changes are required for existing customers to exploit this new capability.
This enhancement complements existing encryption capabilities:
- File system encryption protects MQ data while it is stored on an appliance
- TLS protects MQ data while it is in transit between MQ endpoints
- AMS provides end-to-end encryption for MQ data so it can only be accessed by intended recipients
The MQ Appliance has a small number of dedicated file systems on the RAID storage for configuration, trace, diagnostics, and backups. Each queue manager also has its own dedicated file system for quota management and HA/DR replication. These file systems can be encrypted independently for maximum flexibility, which also helps to stage migration for existing data.
Each file system is assigned a unique volume encryption key, which is protected by a user-specified passphrase that can be changed when required. The passphrase for each file system is automatically stored on the encrypted flash device so it is available to the firmware whenever the file system needs to be mounted, such as at boot or after a HA/DR failover. Passphrases stored on the flash device can also be cleared by an administrator, if required, such as for added protection while an appliance is in transit. A cleared passphrase must then be re-stored on the flash device before the file system can be accessed.
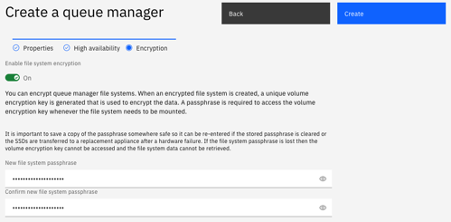
Creating an encrypted file system is easy. Operations that create a file system, such as crtmqm, createbackupfs, and mqrestore support an optional parameter to request encryption. A passphrase for the file system must also be supplied, either interactively, or as a command line parameter. For example, to create a queue manager with an encrypted file system you specify the -fe parameter to crtmqm. The -fp parameter can be used to provide the passphrase if you prefer not to enter it interactively.
crtmqm -fs 10 -fe -fp red-white-blue QM1
or
crtmqm -fs 10 -fe QM1
Enter new file system passphrase:
**************
Re-enter new file system passphrase:
**************
Creating a 10 GB file system for queue manager 'QM1'.
...
Alternatively, you can use the MQ Console, which has also been enhanced to support encrypted queue manager file systems.
In a HA configuration the file system passphrase is automatically stored on both appliances in the HA pair so the file system can be accessed after a fail-over. For disaster recovery, the passphrase must be manually stored on the DR secondary appliance by using the MQ Console, or by using a new setfspass command. The setfspass command is used to manage file system passphrases or schedule an MQ system file system to be encrypted or decrypted. A new dspfspass command is also available that displays status information for file system passphrases, but it cannot be used to display a passphrase itself. For security, passphrases are input only, and they must be remembered by the user.
The dspmq command, the status command, the show qm-status command and the show mq-resources command, have all been enhanced to report whether file systems are encrypted. For example:
mqa(mqcli)# dspmq -o fs
QMNAME(QM1) ENCRYPTED(no)
QMNAME(QM2) ENCRYPTED(yes)
mqa(mqcli)# status QM2
QM(QM2) Status(Running)
CPU: 0.00%
Memory: 195MB
Queue manager file system: 3.0GB total, 134MB used [4%] [encrypted]
Their REST equivalents also report the same information, such as:
GET /ibmmq/rest/v2/admin/qmgr?attributes=extended
{
'qmgr': [
{
"name": "QM1",
"state": "endedImmediately",
"extended": {
"installationName": "MQAppliance",
"isDefaultQmgr": false,
"encryptedFileSystem": "no"
}
},
{
"name": "QM2",
"state": "running",
"extended": {
"installationName": "MQAppliance",
"isDefaultQmgr": false,
"encryptedFileSystem": "yes"
}
}
]
}
You cannot encrypt or decrypt an existing queue manager file system in-place, but you can backup the queue manager, then restore it to a new file system by using the mqrestore command. The mqrestore command can be used to allocate either an encrypted or an unencrypted file system, as required. Encrypted file systems are a little smaller than their unencrypted equivalent, so you can now restore a queue manager backup to a larger file system if you need to. You can also restore a queue manager backup to a smaller file system, provided it is still large enough to store the queue manager data. This new ability provides a method to reduce the size of a queue manager file system, given a file system can only be extended in-place by using the setmqsize command. It is also important to note that queue manager backup files are not themselves encrypted. Therefore, when backing up or restoring a queue manager with an encrypted file system, ensure the queue manager backup file system (created by the createbackupfs command) is also encrypted. File system encryption only protects data that is stored on the appliance disks, so if a backup file is copied to a remote system, then ensure appropriate security measures are in place.
For more information about encrypted file systems on the MQ Appliance see the product documentation at https://www.ibm.com/docs/en/mq-appliance/9.2?topic=security-file-system-encryption.
We have also published a whitepaper that illustrates the overhead of using this encryption capability. There is a small increase in CPU that reflects the cost of encryption and decryption, although MQ optimises message retrieval from disk. There is also an increase in latency for disk IO that reflects the additional processing. Using multiple queue managers to achieve parallelisation can help to reduce the impact of this increased latency, if required. The whitepaper can be found at https://ibm-messaging.github.io/mqperf/M2002_9.2.5_Encrypted_Filesystem_Impact.pdf.
#Encryption#IBMMQ#MQ#mqappliance