The purpose of this blog is to provide step-by-step guide to setting up a Salesforce OpenID Namespace by creating a Salesforce Openid Client and then configuring Cognos Analytics 11 to successfully authenticate. There will be both the native as well as the generic namespaces setup.
Environment:
Windows 2016
Cognos Analytics 11.1
AD Domain: casupport.support2016.ad.hursley.ibm.com
Salesforce Domain: https://ibmcasupport-dev-ed.lightning.force.com
Note: It will be assumed that the reader will already have the Salesforce Domain setup first.
Section 1:Steps are as follows:
1. Log into your Salesforce Domain and from the toolbar click on "Setup"
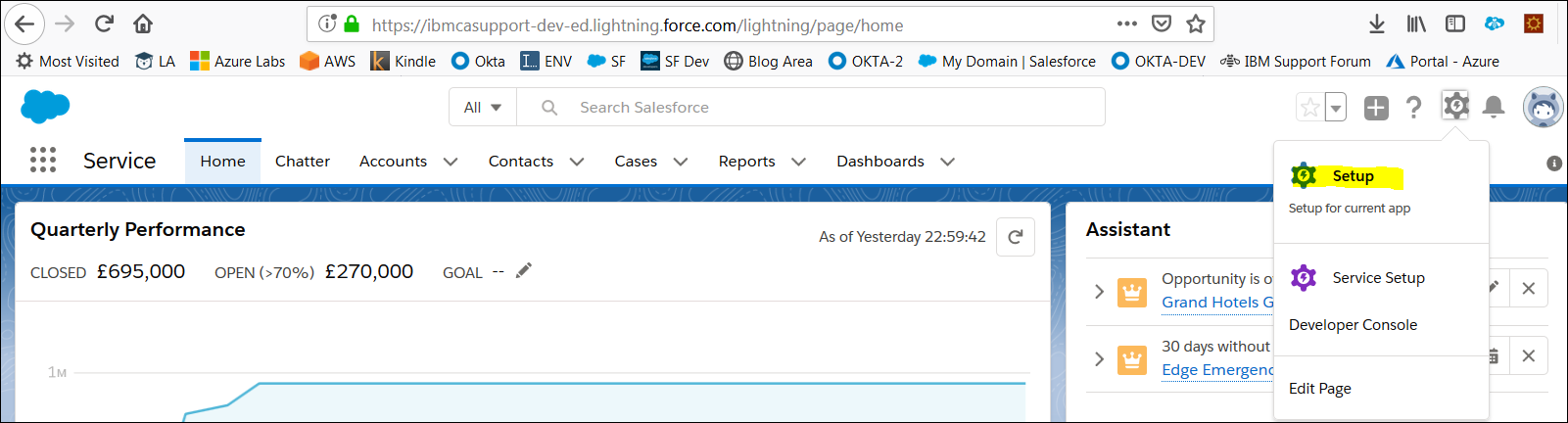
2. On the right list click on Apps/App Manager
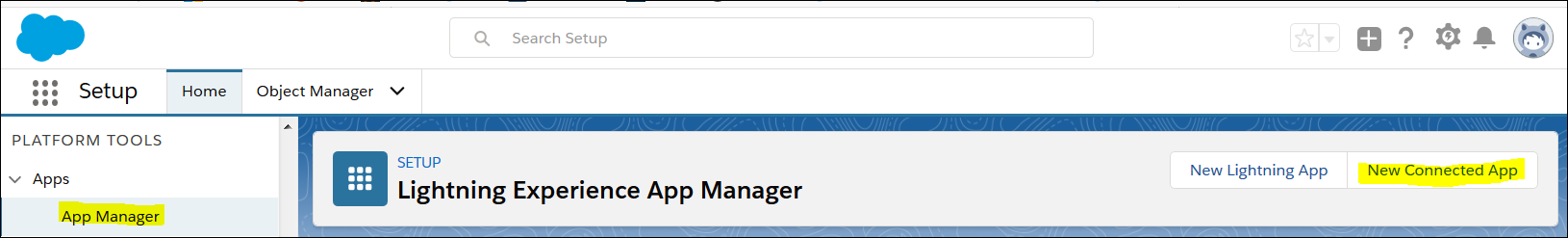
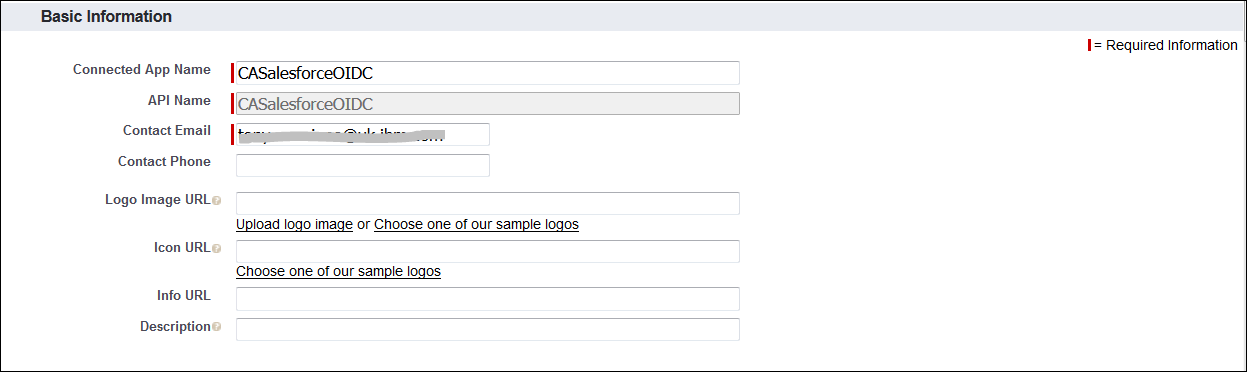
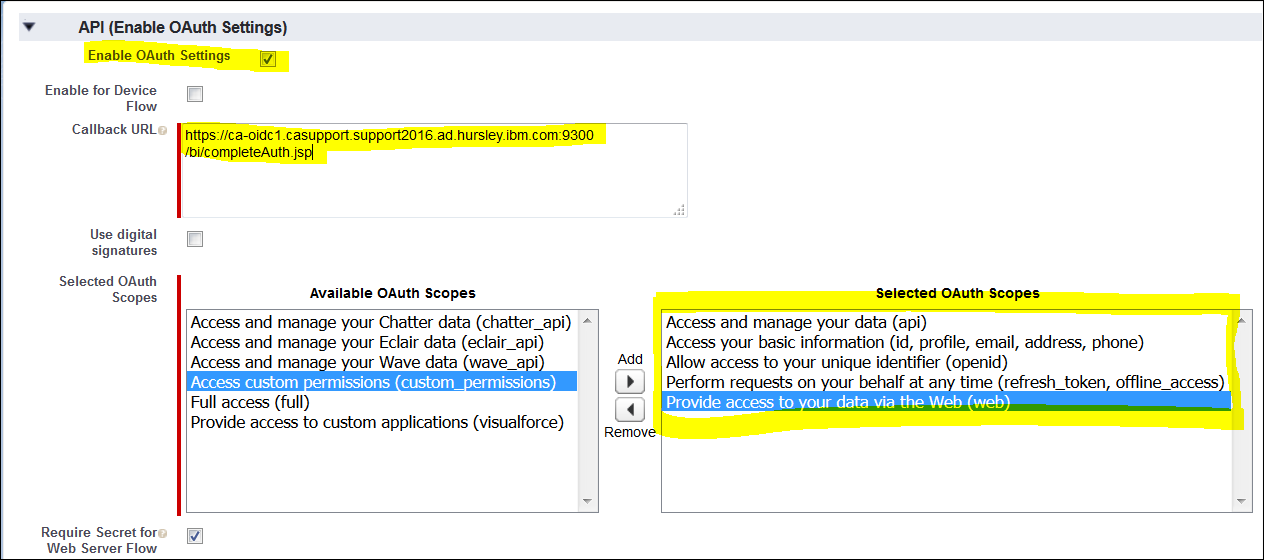
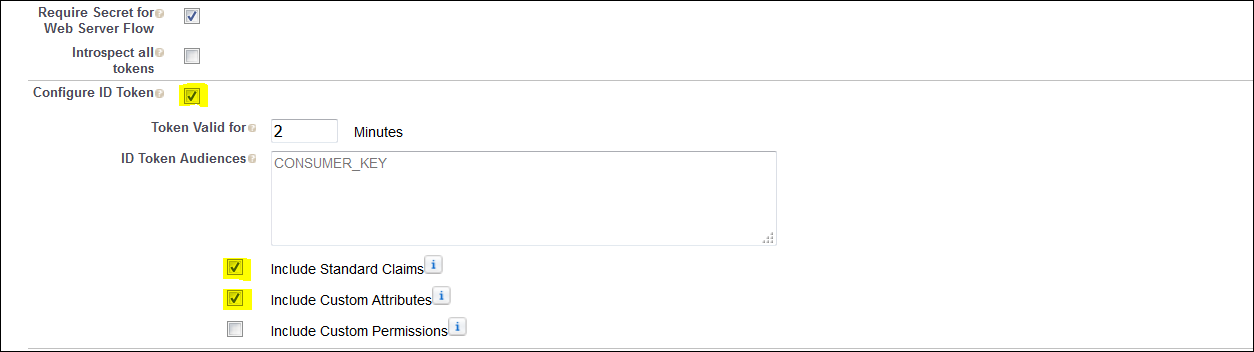
3. Click on "New Connected App" and fill in the following details:
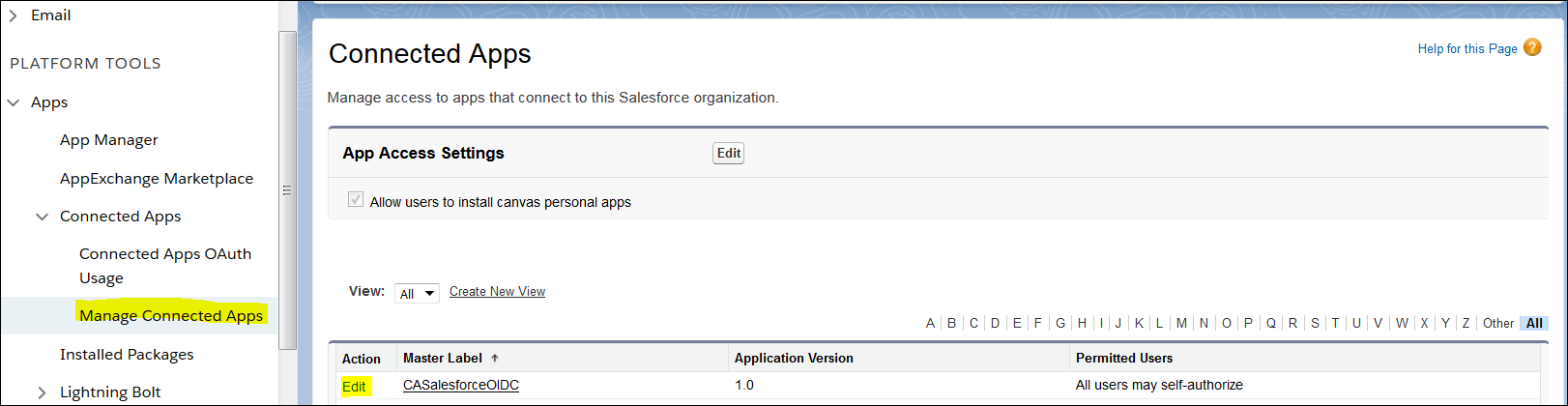
4. Click "Save" and then click on "Manage Connected Apps" and next to the newly created App click "Edit"
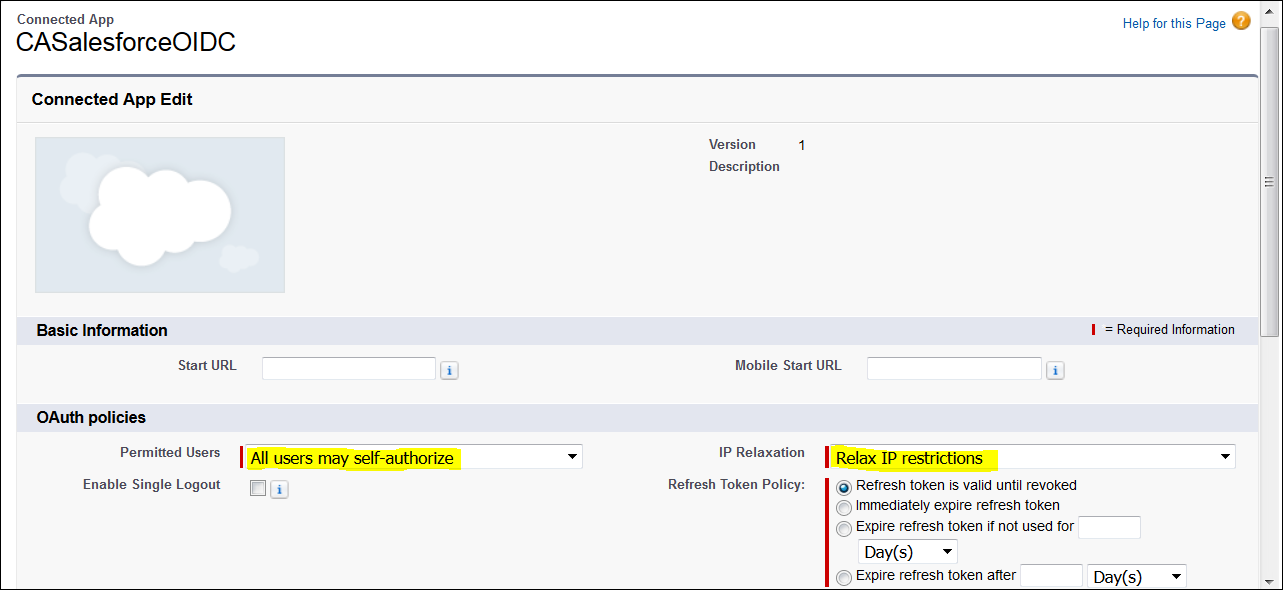
5. Edit the following OAuth Policy Settings and then click "Save":
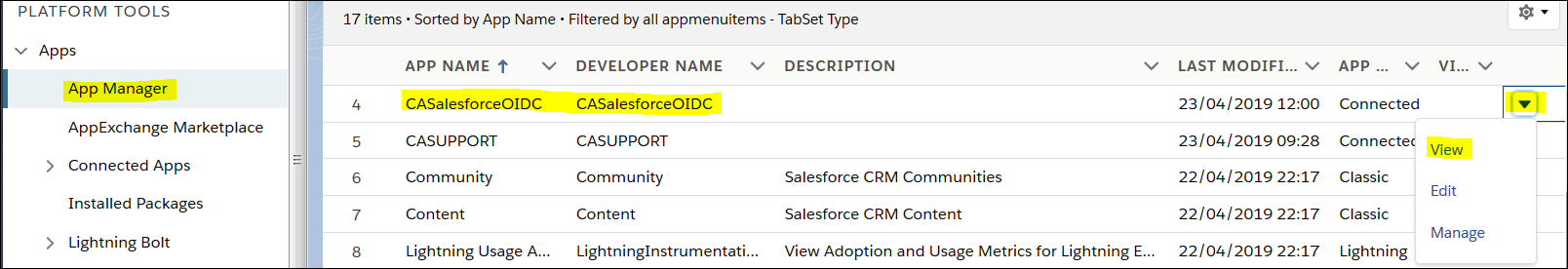
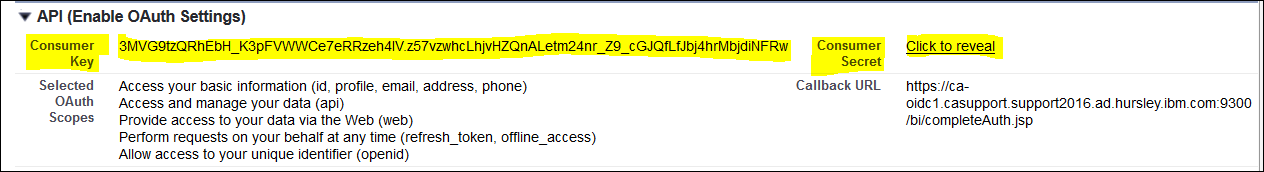
6. To expose the Client ID/Client Secret Information click on "View" next to the App
7. To reveal the Client (Consumer) Secret click on "Click to reveal" link
 Section 2:
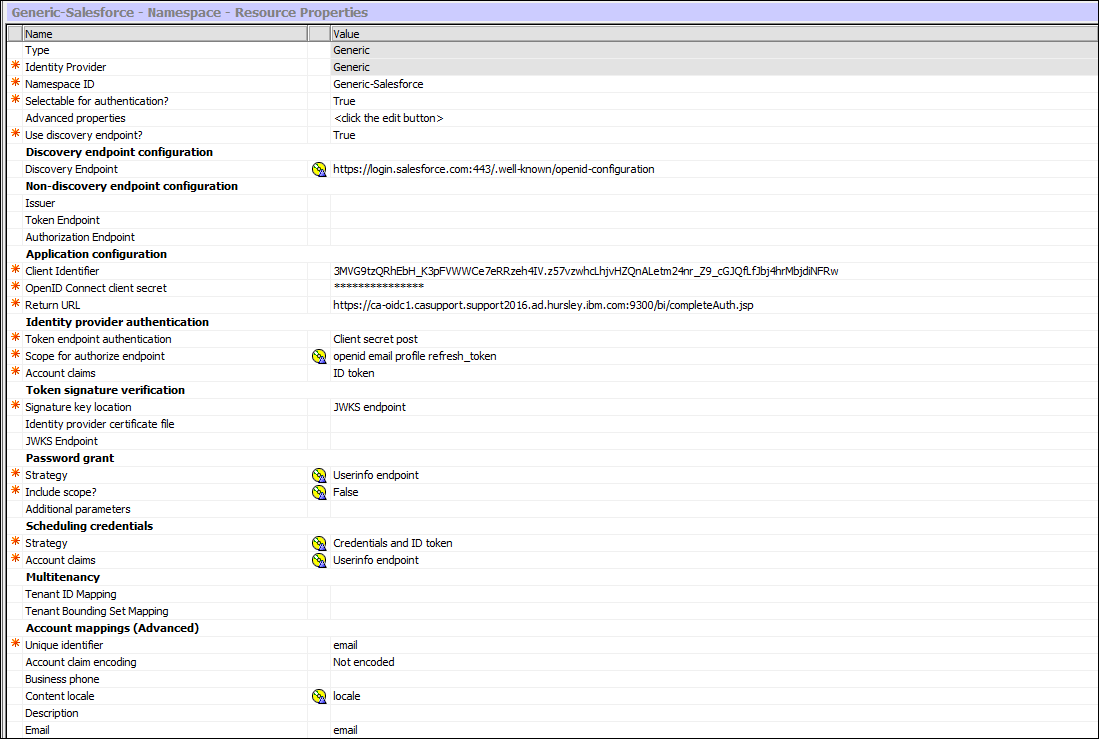
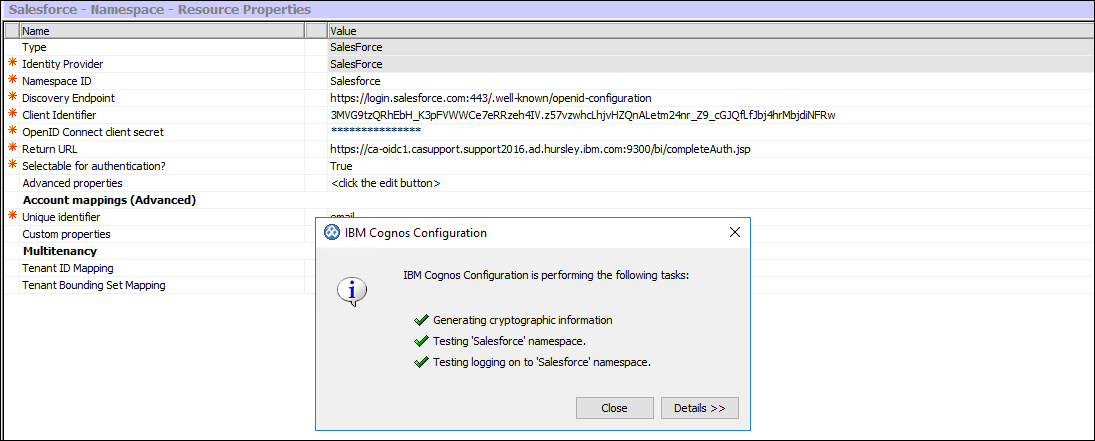
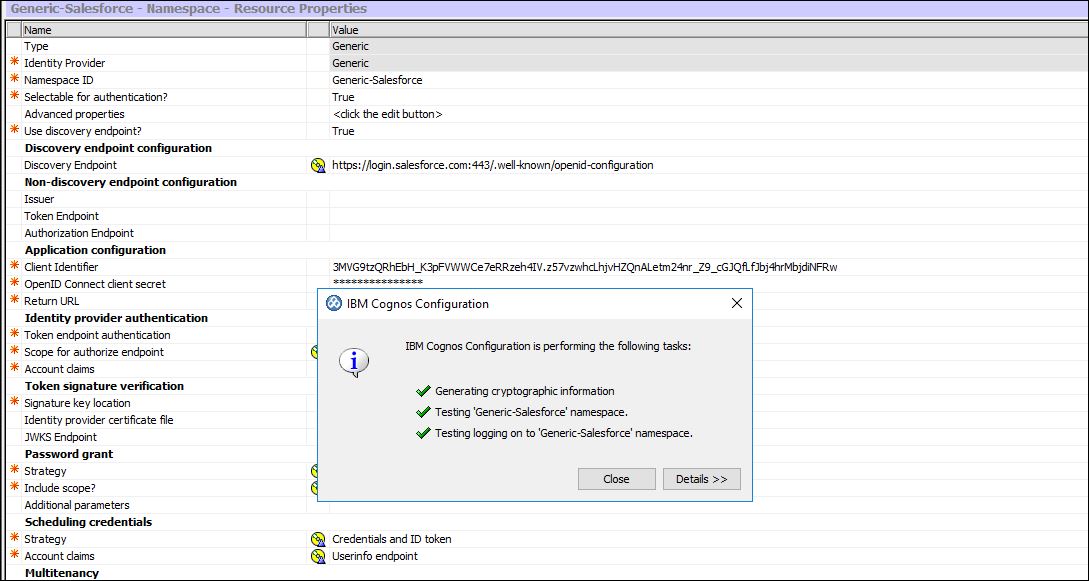
Section 2:Setup the Cognos Analytics Salesforce OpenID Namespace and the equivalent Generic Namespace
Details required (based on my lab):
Discovery Endpoint URL: https://login.salesforce.com:443/.well-known/openid-configuration
Client ID(Consumer Key) + Client Secret (Consumer Secret)
Redirect URL : https://ca-oidc1.casupport.support2016.ad.hursley.ibm.com:9300/bi/completeAuth.jsp
8. Download the Root CA Certificate to the CA /bin directory :
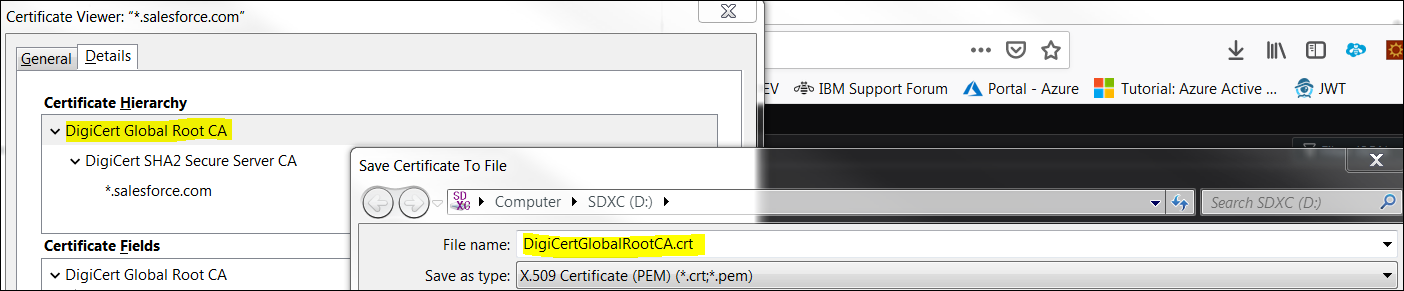
9. Import the certificate into the KeyStore:
<Cognos Anaytics Installation>/bin/ThirdpartyCertTool.bat -i -T -r DigiCertGlobalRootCA.crt -p NoPassWordSet
10. Launch Cognos Configuration
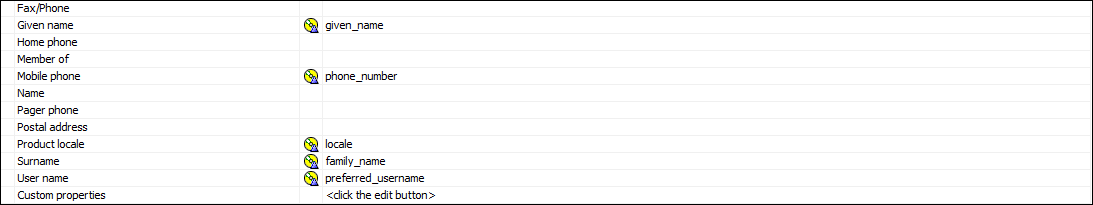
Salesforce Openid Namespace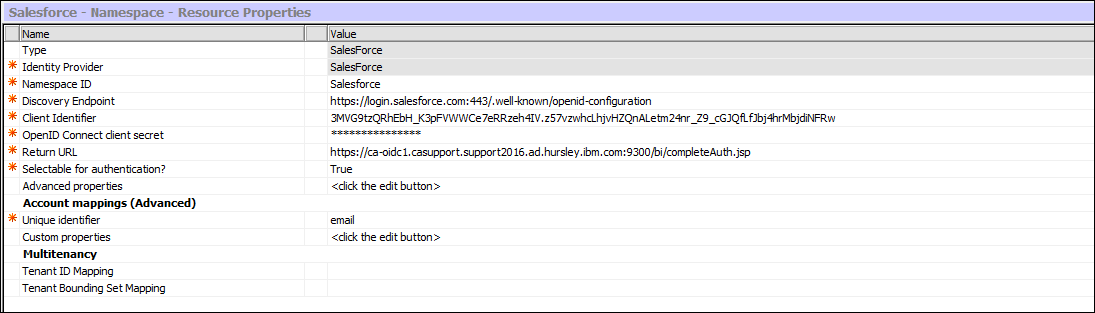 Generic OpenID Namespace for Salesforce:
Generic OpenID Namespace for Salesforce:
11. Save and make sure the test succeeds:
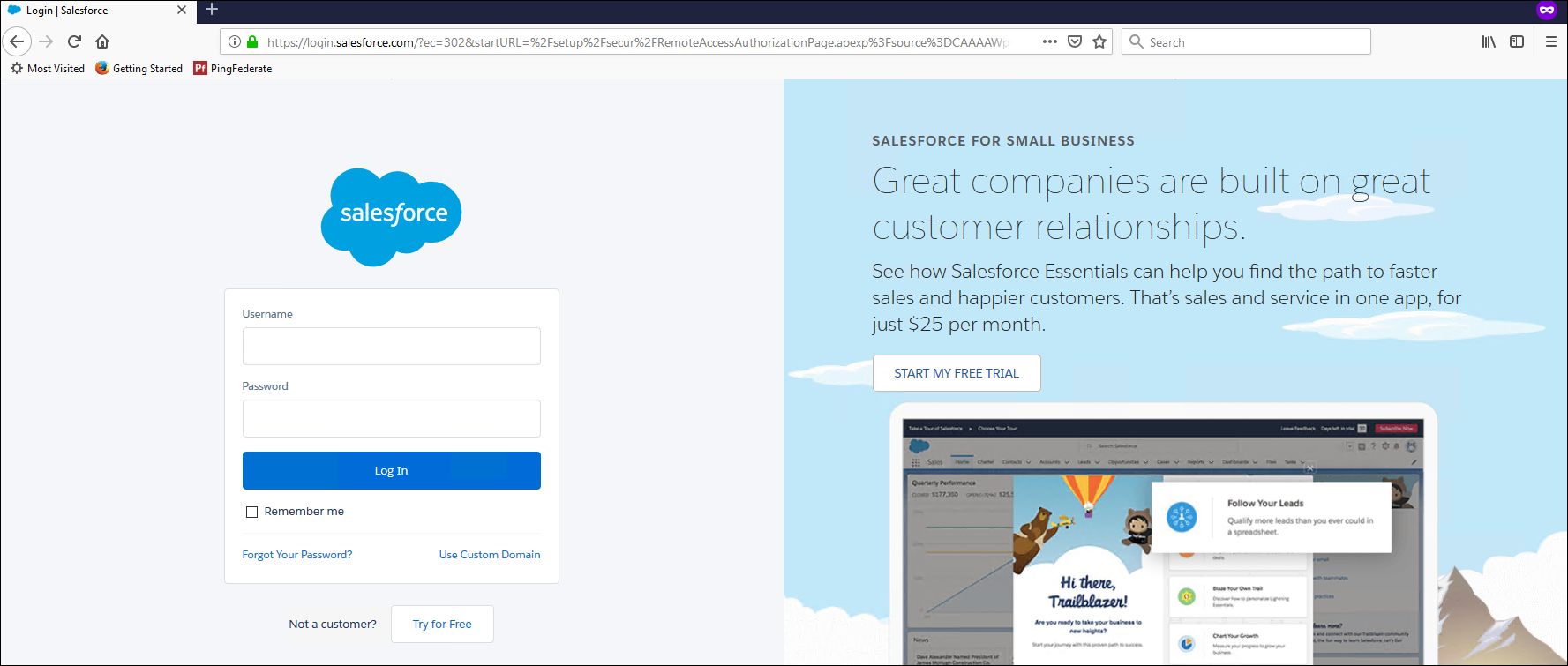
12. Restart and log in
 Additional Information:
In 11.1.4+ there are 4 new advanced configuration items:
Additional Information:
In 11.1.4+ there are 4 new advanced configuration items:
name
authorizeEPAddParms (authorize redirect)
pgTokenEPAddParms (on password grant flow to the token endpoint)
rtTokenEPAddParms (on refresh token flow to the token endpoint)
codeTokenEPAddParms (on authorization code flow to the token endpoint)
This allows you to control exactly what addition parameters are added and specifically to which endpoints. Given the "resource" parameter could be represented using the new advanced configuration items, the value let's you put whatever you want in the URL... as a consequence, the value must include the &, the parameter name, and the parameter value which MUST be url encode e.g.
name value
authorizeEPAddParms &resource=HTTPS%3A%2F%2FADFS_SERVER#Administration#CognosAnalyticswithWatson#home#LearnCognosAnalytics