CVE-2021–40444 MSHTML vulnerability (RCE)
How it Works
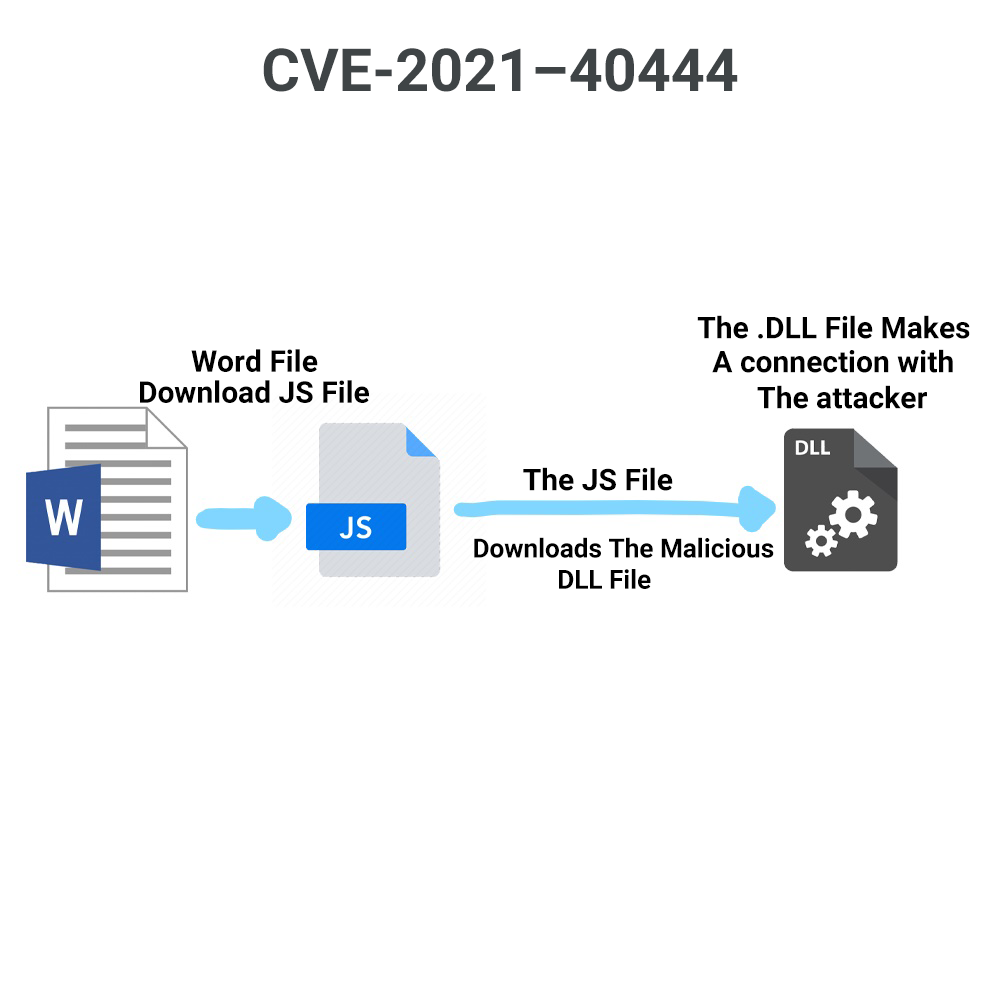
A Microsoft word file downloads a javascript file, and that javascript file downloads a . DLL file and the DLL file open a connection with the attacker using cobalt strike, all of this happens using the Microsoft word macros (Microsoft already released a patch)
DLL File: A DLL is a library that contains code and data that can be used by more than one program at the same time. For example, in Windows operating systems, the Comdlg32 DLL performs common dialog box-related functions. Each program can use the functionality that is contained in this DLL to implement an Open dialog box.
Macros: Macros are a powerful way to automate common tasks in Microsoft Office and can make people more productive. However, macro malware uses this functionality to infect your device.
CobaltStrike: Cobalt Strike gives you a post-exploitation agent and covert channels to emulate a quiet long-term embedded actor in your customer's network. Malleable C2 lets you change your network indicators to look like different malware each time. These tools complement Cobalt Strike's solid social engineering process, its robust collaboration capability, and unique reports designed to aid blue team training.
For more Technical information you can read the Official Blog, My Blog, PoC
------------------------------
Noureldin Ehab
Software Engineering Student | Cyber Security Enthusiast | Red Team 🔴 | CTF Addict 👾
Twitter:https://twitter.com/Nouureldin_Ehab
Linkedin:https://www.linkedin.com/in/noureldin-ehab-a57940190/
------------------------------