Introduction
This document describes how to deploy bastion infrastructure services for IBM zCX Foundation for Red Hat OpenShift or IBM zCX for OpenShift1 (zCX for OCP). For more information about zCX for OpenShift, see the content solution page.
Red Hat OpenShift Infrastructure services
Red Hat OpenShift infrastructure services are prerequisites for installing a Red Hat OpenShift cluster on pre-existing infrastructure. These prerequisites are the same on all platforms where Red Hat OpenShift cluster deployments are supported. For more details on the Red Hat OpenShift infrastructure services, refer to IBM zCX for OpenShift documentation.
IBM zCX for OpenShift supports only user-provisioned infrastructure deployment. Most IT installations will have their own solutions for OpenShift infrastructure services that they can either extend or leverage for Red Hat OpenShift cluster installation on zCX.
These services can be optionally deployed on a Classic zCX appliance instance (that is, a Docker appliance) and leveraged as the bastion node for the zCX for OpenShift cluster installation. These services will be deployed as containerized software components.
An example of Bastion Infrastructure Service setup for the OpenShift cluster is shown below.
This capability is useful when planning for a quick prototype or PoC, and don’t want to update the existing infrastructure services for the zCX OpenShift cluster. Deploying OpenShift infrastructure services in a Classic zCX instance provides a self-contained z/OS-only solution that can be used for prototype purposes.
The key thing to note here is that these are containerized software deployments of the above infrastructure services that do not provide high availability (HA), redundancy, or optimal performance. Therefore, they are not recommended for production use.
To leverage a Classic zCX appliance instance as the bastion node for zCX for OpenShift installation, you need to purchase and install IBM Container Hosting Foundation for z/OS or activate the 90-day zCX Trial. Alternatively, if you have an IBM z14 or IBM z15 processor, you can purchase and install feature code 0104 (IBM Container Hosting Foundation) through the eConfig Fulfillment Center.
Classic zCX requirements for zCX for OpenShift bastion node
Provision and start a Classic zCX appliance instance using the zCX z/OSMF provision workflow to use as a bastion node and to deploy Red Hat OpenShift infrastructure services for your prototype program validation efforts.
System requirements:
CPU
|
4
|
Memory
|
16GB
|
Disks
|
30GB
|
Network
|
1 DVIPA address
|
Deploy Red Hat OpenShift Infrastructure services
Manually deploy Red Hat OpenShift infrastructure services as Docker containers in the Classic zCX appliance instance. The following open-source components can be downloaded, configured, and deployed as bastion infrastructure services for Red Hat OpenShift Cluster deployment on zCX:
-
Apache HTTPD container image as the HTTP file hosting server
-
BIND container image as the DNS server
-
HAProxy container image as the load-balancer
-
Red Hat OpenShift Installer program and OpenShift CLI utility program can be installed, configured, and run inside a separate container image
To expedite the manual Red Hat OpenShift infrastructure services deployments in a Classic zCX instance for prototype purposes, a bastion node helper Docker image is provided in the IBM Container Registry (ICR) that can be downloaded and used to automate the deployment of Red Hat OpenShift infrastructure services in a Classic zCX instance.
This helper container image can be downloaded from the ICR and deployed in the Classic zCX instance to automate the deployment of all the above infrastructure services and Red Hat OpenShift utilities in Classic zCX as containers.
In a typical deployment scenario, a user often has a proxy between their cluster and the public network. In such a case, set the proxy.http_proxy and proxy.https_proxy value in the bastion.yml, using the format of http(s)://<proxy_server>:<port>.
Step-by-step guide
- Log in to IBM Container Registry (icr.io) in order to pull the bastion helper image.
- Navigate through Manage > Access (IAM) and view “My IBM Cloud API Keys” in the bottom-center of the page to obtain your API key
- Issue $ docker login icr.io -u iamapikey -p your_api_key
- Verify Login Succeeded is returned from the docker login command
- Set the zCX bastion helper container image sha256 value in the current session. The current hash value may be different due to the newer build for the security update.
- export HELPER_SHA=c9d604ad81235b5b0225c9a7eac664757b637b85466f4bdbc3376fe1567488c7
- Pull the bastion helper container image from the icr.io on zCX or upload on to the Classic zCX appliance instance if the image is pulled somewhere else.
- $ docker pull icr.io/ibmz/zcx-bastion-helper@sha256:${HELPER_SHA}
- Run the following command to deploy the bastion helper container on the Classic zCX appliance instance:
- $ docker run --name helper -it -v /var/run/docker.sock:/var/run/docker.sock -v helper-vol:/data icr.io/ibmz/zcx-bastion-helper@sha256:${HELPER_SHA} bash
- Verify helper container is successfully created and the user is logged in with bash
- Run the following command to view the help/usage guidance when you need a reference:
- Modify the sample input file called bastion.yml in the default location to configure the bastion infrastructure services
- $ vim /home/zcxocp/ansible/bastion.yml
- Provide the zCX OCP cluster name, domain name, DNS servers to use, zCX DVIPA addresses for the zCX OCP cluster nodes, URL to download the Red Hat OCP binaries, and the pull secret.
- Make sure to update the RH OCP version number to 4.10.* in the RH ocp_xxxx parameters’ link.
- Make sure to fill out the OCP pull secret.
- It is best practice to not have the last octet of the instance IP overlaps each other if you have multiple subnets listed in the resolve_ip section in the bastion.yml.
- Login to icr.io again inside the helper container, refer to step 1. This is a required step before executing step 7.
- Run the following command to deploy the services in containers:
- $ deploy
- This command should only be issued once the bastion.yml file is updated with Cluster information
- Verify the deployment task has been successfully completed.

- Verify the status of the bastion infrastructure services:
- There should be four containers (zcxocp-xxx) deployed and in running state
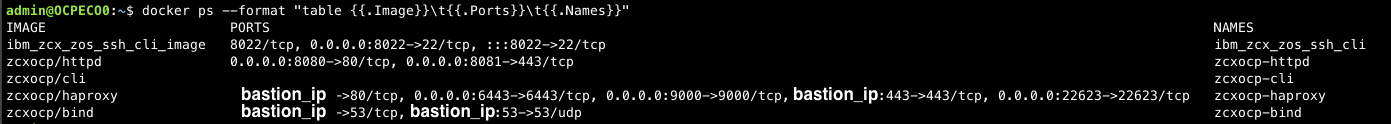
- Container description for referencing:
- zcxocp-httpd: a file hosting server that serves OCP ignition and binary files thru ports 8080(HTTP) and 8081 (HTTPS)
- zcxocp-cli: the OCP command line interface utility container that use to generate install configuration and access cluster
- zcxocp-haproxy: software-defined cluster traffic load-balancer
- zcxocp-bind: software-defined cluster endpoint DNS resolver
- Verify ignition files have been created and served on the file server by checking the http://bastion_ip:8080/ignition, there should be one ignition for each bootstrap, control, and compute node.

- Red Hat OpenShift binaries for the requested OCP version are also backed up and served on the http://bastion_ip:8080/install
- Provide the fully qualified URL information in the zCX OCP provision workflow (in z/OSMF Workflow)

Provision of Red Hat OpenShift cluster on zCX
Refer to z/OS Management Facility workflows for zCX for OpenShift documentation for more details on provisioning workflow and to continue the cluster provision process.
Tearing down the Bastion node services on zCX
Once the zCX OCP deprovision workflow is completed successfully to deprovision the zCX OCP cluster instances, bastion infrastructure services can be removed from the Classic zCX instance.
If bastion infrastructure services are removed while the cluster is operational, without explicitly backup of the cluster authentication data, access to the OCP cluster is removed and cannot be restored.
To remove the Red Hat OpenShift infrastructure services deployed in the Classic zCX appliance instance (bastion node):
- Back up the cluster-related data that is listed in the helper message
- Run the following command inside the helper container
-
- Confirm "y/Y" when prompted to continue
- Run the following command to remove the zcx-bastion-helper container and the container image:
Update
| Date |
Content |
| Mar/15/2025 |
Updated s390x/bind base image to fix vulnerabilities and add dependency to support for newer OC cli.
User action: In the bastion.yml -> hosts -> vars -> misc -> bind_image, replace the image sha256 value with e33fafd45e35024980cae156f2df7eac3fd6bd2b62417c41223ac9978d9a55ca
|
References
- IBM zCX Foundation for Red Hat Foundation. https://www.ibm.com/products/zcx-openshift
- Red Hat OpenShift. https://www.Red Hat.com/en/technologies/cloud-computing/openshift
- zCX Foundation for Red Hat OpenShift content solution. https://www.ibm.com/support/z-content-solutions/zcx-openshift
Acknowledgments
Ahilan Rajadeva, IBM, STSM – z/OS Container Extensions. rajadeva@us.ibm.com
Bill Keller, IBM, Content Designer-Systems. bkeller@us.ibm.com